IAPP Certified Information Privacy Technologist CIPT Exam Questions
Which of the following most embodies the principle of Data Protection by Default?
Answer : D
Data Protection by Default is about ensuring that, by default, only necessary personal data is processed for each specific purpose and that the highest privacy settings are applied automatically. The scenario where a website uses an opt-in form for marketing emails reflects this principle because it ensures that users must actively consent to their data being used for marketing purposes, rather than having it enabled by default.
IAPP Certification Textbooks: 'Data Protection by Default' principles require that users are given control over their data and that only essential data is processed by default.
What is an Access Control List?
Answer : C
Option A: Decentralization of data typically increases the complexity of access controls as data is spread across various locations and systems.
Option B: Regular data inventories help understand what data exists and where it is stored, but they do not directly reduce the need for different types of access controls.
Option C: Standardization of technology simplifies the IT environment, making it easier to implement and manage consistent access controls across the organization.
Option D: An increased number of remote employees generally requires more robust and varied access controls to manage the different ways remote access is secured.
IAPP CIPT Study Guide
Best practices for access control management in IT systems
Which of the following statements best describes the relationship between privacy and security?
Answer : A
Security systems are essential for protecting data and ensuring that privacy policies are followed. Effective security measures can enforce access controls, encryption, and other protections that help maintain data confidentiality, integrity, and availability. By implementing robust security systems, organizations can ensure that personal information is handled according to privacy policies and regulatory requirements. The IAPP highlights that security is a foundational component for achieving privacy compliance.
IAPP Certification Textbooks, specifically the sections on the relationship between privacy and security.
'Privacy and Data Protection: An Integrated Approach,' IAPP White Paper.
When should code audits be concluded?
Answer : D
Code audits should be concluded before the launch, after all code for a feature is complete. This practice ensures that the entire codebase has been thoroughly reviewed and tested for security vulnerabilities and compliance with privacy standards before it is deployed to production. Conducting a comprehensive audit at this stage helps identify and address any issues that could compromise the integrity, security, or privacy of the system. This approach aligns with best practices in software development and is supported by guidelines from the IAPP and other industry standards, which recommend finalizing code audits as part of the pre-launch quality assurance process.
Which activity best supports the principle of data quality from a privacy perspective?
Answer : D
Principle of Data Quality: Data quality refers to the accuracy, completeness, and reliability of data.
Unauthorized Changes: Ensuring data is protected against unauthorized changes maintains its integrity, which is a key aspect of data quality.
Implementation: Measures like access controls, audit logs, and regular data integrity checks are essential to protect data from unauthorized modifications.
Reference: IAPP CIPT Study Guide, Chapter on Data Quality and Integrity.
SCENARIO
Clean-Q is a company that offers house-hold and office cleaning services. The company receives requests from consumers via their website and telephone, to book cleaning services. Based on the type and size of service, Clean-Q then contracts individuals that are registered on its resource database - currently managed in-house by Clean-Q IT Support. Because of Clean-Q's business model, resources are contracted as needed instead of permanently employed.
The table below indicates some of the personal information Clean-Q requires as part of its business operations:
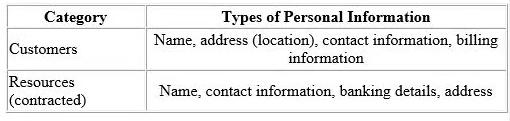
Clean-Q has an internal employee base of about 30 people. A recent privacy compliance exercise has been conducted to align employee data management and human resource functions with applicable data protection regulation. Therefore, the Clean-Q permanent employee base is not included as part of this scenario.
With an increase in construction work and housing developments, Clean-Q has had an influx of requests for cleaning services. The demand has overwhelmed Clean-Q's traditional supply and demand system that has caused some overlapping bookings.
Ina business strategy session held by senior management recently, Clear-Q invited vendors to present potential solutions to their current operational issues. These vendors included Application developers and Cloud-Q's solution providers, presenting their proposed solutions and platforms.
The Managing Director opted to initiate the process to integrate Clean-Q's operations with a cloud solution (LeadOps) that will provide the following solution one single online platform: A web interface that Clean-Q accesses for the purposes of resource and customer management. This would entail uploading resource and customer information.
A customer facing web interface that enables customers to register, manage and submit cleaning service requests online.
A resource facing web interface that enables resources to apply and manage their assigned jobs.
An online payment facility for customers to pay for services.
Considering that LeadOps will host/process personal information on behalf of Clean-Q remotely, what is an appropriate next step for Clean-Q senior management to assess LeadOps' appropriateness?
Answer : D
Given that LeadOps will host/process personal information on behalf of Clean-Q remotely, it is crucial to involve the Information Security team to understand in more detail the types of services and solutions LeadOps is proposing.
Security Assessment: The Information Security team should evaluate LeadOps' security measures, data protection practices, and compliance with relevant regulations. This assessment ensures that the service provider has adequate safeguards to protect personal information.
Risk Management: Understanding the security environment helps identify potential risks associated with outsourcing data processing. This includes assessing encryption practices, data storage policies, and incident response plans.
Legal and Compliance Considerations: Involving the Information Security team ensures that Clean-Q adheres to data protection regulations such as GDPR or CCPA, which require businesses to ensure their processors provide adequate data protection.
IAPP Privacy Management, Information Privacy Technologist Certification Textbooks
ISO/IEC 27001 -- Information Security Management Systems
GDPR Articles 28 and 32
In day to day interactions with technology, consumers are presented with privacy choices. Which of the following best represents the Privacy by Design (PbD) methodology of letting the user choose a non-zero-sum choice?
Answer : B
Option A: While using positive imagery and language can influence user behavior, it doesn't specifically address the principle of non-zero-sum choices, which are about providing meaningful privacy choices that do not require users to sacrifice one benefit for another.
Option B: This option aligns with the Privacy by Design (PbD) principle of empowering users with clear, understandable choices that allow them to protect their privacy without facing undue complexity or negative consequences. This reflects a non-zero-sum approach where privacy is integrated seamlessly and transparently into the user experience.
Option C: Displaying what other users chose can create a herd effect but does not inherently relate to non-zero-sum choices, which are about giving users meaningful and balanced privacy options.
Option D: Using priming techniques can assist in decision-making but does not specifically address the principle of non-zero-sum choices.
IAPP CIPT Study Guide
Privacy by Design Framework