ISC2 Certified Secure Software Lifecycle Professional CSSLP Exam Questions
You are advising a school district on disaster recovery plans. In case a disaster affects the main IT centers for the district they will need to be able to work from an alternate location. However, budget is an issue. Which of the following is most appropriate for this client?
Answer : A
A cold site provides an office space, and in some cases basic equipment. However, you will need to restore your data to that equipment in
order to use it. This is a much less expensive solution than the hot site.
Answer D is incorrect. A hot site has equipment installed, configured and ready to use. This may make disaster recovery much faster,
but will also be more expensive. And a school district can afford to be down for several hours before resuming IT operations, so the less
expensive option is more appropriate.
Answer C is incorrect. A warm site is between a hot and cold site. It has some equipment ready and connectivity ready. However, it is
still significantly more expensive than a cold site, and not necessary for this scenario.
Answer B is incorrect. Off site is not any type of backup site terminology.
Which of the following ensures that a party to a dispute cannot deny the authenticity of their signature on a document or the sending of a message that they originated?
Answer : D
Non-repudiation is a term that refers to the ability to ensure that a party to a dispute cannot deny the authenticity of their signature on a
document or the sending of a message that they originated.
Non-repudiation is the concept of ensuring that a party in a dispute cannot refuse to acknowledge, or refute the validity of a statement or
contract. As a service, it provides proof of the integrity and origin of data. Although this concept can be applied to any transmission, including
television and radio, by far the most common application is in the verification and trust of signatures.
Answer A is incorrect. Confidentiality is a mechanism that ensures that only the intended and authorized recipients are able to read
data. The data is so encrypted that even if an unauthorized user gets access to it, he will not get any meaning out of it.
Answer C is incorrect. Reconnaissance is a term that refers to information gathering behaviors that aim to profile the organization,
employees, network, and systems before an attack is performed efficiently. It is the first step in the process of intrusion and involves
unauthorized discovery and mapping of systems, services, or vulnerabilities. These discovery and mapping techniques are commonly known as
scanning and enumeration. Common tools, commands, and utilities used for scanning and enumeration include ping, telnet, nslookup, rpcinfo,
File Explorer, finger, etc.
Reconnaissance activities take place before performing a malicious attack. These activities are used to increase the probability of successful
operation against the target, and to increase the probability of hiding the attacker's identity.
Answer B is incorrect. OS fingerprinting is a process in which an external host sends special traffic on the external network interface of
a computer to determine the computer's operating system. It is one of the primary steps taken by hackers in preparing an attack.
Which of the following statements about the authentication concept of information security management is true?
Answer : A
The concept of authentication establishes the users' identity and ensures that the users are who they say they are.
Answer B is incorrect. The concept of availability ensures the reliable and timely access to data or resources.
Answer D is incorrect. The concept of integrity ensures that modifications are not made to data by unauthorized personnel or
processes.
Answer C is incorrect. The concept of accountability determines the actions and behaviors of a single individual within a system, and
identifies that particular individual.
Which of the following security issues does the Bell-La Padula model focus on?
Answer : B
The Bell-La Padula model is a state machine model used for enforcing access control in large organizations. It focuses on data confidentiality
and access to classified information, in contrast to the Biba Integrity model, which describes rules for the protection of data integrity. In the
Bell-La Padula model, the entities in an information system are divided into subjects and objects.
The Bell-La Padula model is built on the concept of a state machine with a set of allowable states in a computer network system. The
transition from one state to another state is defined by transition functions. The model defines two mandatory access control (MAC) rules and
one discretionary access control (DAC) rule with three security properties:
1.The Simple Security Property: A subject at a given security level may not read an object at a higher security level (no read-up).
2.The *-property (star-property): A subject at a given security level must not write to any object at a lower security level (no write-
down). The *-property is also known as the Confinement property.
3.The Discretionary Security Property: It uses an access matrix to specify the discretionary access control.
Single Loss Expectancy (SLE) represents an organization's loss from a single threat. Which of the following formulas best describes the Single Loss Expectancy (SLE)?
Answer : A
Single Loss Expectancy is a term related to Risk Management and Risk Assessment. It can be defined as the monetary value expected from
the occurrence of a risk on an asset. It is mathematically expressed as follows:
Single Loss Expectancy (SLE) = Asset Value (AV) * Exposure Factor (EF)
where the Exposure Factor is represented in the impact of the risk over the asset, or percentage of asset lost. As an example, if the Asset
Value is reduced two thirds, the exposure factor value is .66. If the asset is completely lost, the Exposure Factor is 1.0. The result is a
monetary value in the same unit as the Single Loss Expectancy is expressed.
Answer C, D, and B are incorrect. These are not valid formulas of SLE.
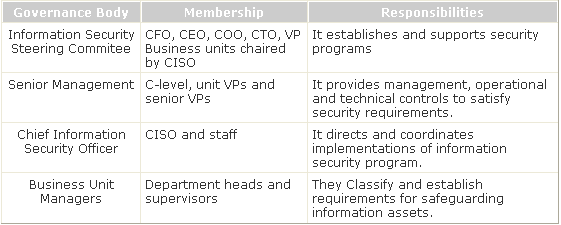
Which of the following governance bodies directs and coordinates implementations of the information security program?
Answer : A
Chief Information Security Officer directs and coordinates implementations of the information security program.
The governance roles and responsibilities are mentioned below in the table:
Which of the following sections come under the ISO/IEC 27002 standard?
Answer : A, B, D
ISO/IEC 27002 is an information security standard published by the International Organization for Standardization (ISO) and by the
International Electrotechnical Commission (IEC) as ISO/IEC 17799:2005.
This standard contains the following twelve main sections:
1.Risk assessment: It refers to assessment of risk.
2.Security policy: It deals with the security management.
3.Organization of information security: It deals with governance of information security.
4.Asset management: It refers to inventory and classification of information assets.
5.Human resources security: It deals with security aspects for employees joining, moving and leaving an organization.
6.Physical and environmental security: It is related to protection of the computer facilities.
7.Communications and operations management: It is the management of technical security controls in systems and networks.
8.Access control: It deals with the restriction of access rights to networks, systems, applications, functions and data.
9.Information systems acquisition, development and maintenance: It refers to build security into applications.
10.Information security incident management: It refers to anticipate and respond appropriately to information security breaches.
11.Business continuity management: It deals with protecting, maintaining and recovering business-critical processes and systems.
12.Compliance: It is used for ensuring conformance with information security policies, standards, laws and regulations.
Answer C is incorrect. Financial assessment does not come under the ISO/IEC 27002 standard.