Juniper Data Center Design, Specialist Exam JN0-1302 JNCDS-DC Exam Questions
Which two scripting languages are supported for creating on-box scripts? (Choose two.)
Answer : B, C
You are designing an EVPN/VXLAN overlay network for your data center. You are planning on reusing some of your existing devices that do not support VXLAN routing.
Which gateway model should be deployed to support this architecture?
Answer : A
You must implement high availability features in the design for a data center Every network device in this design will have dual routing engines In this scenario, which two high availability features should you use? (Choose two )
Answer : A, B
Which two characteristics describe a one-arm firewall deployment? (Choose two )
Answer : B, C
What are two reasons for using cRPD? (Choose two.)
Answer : A, D
Exhibit.
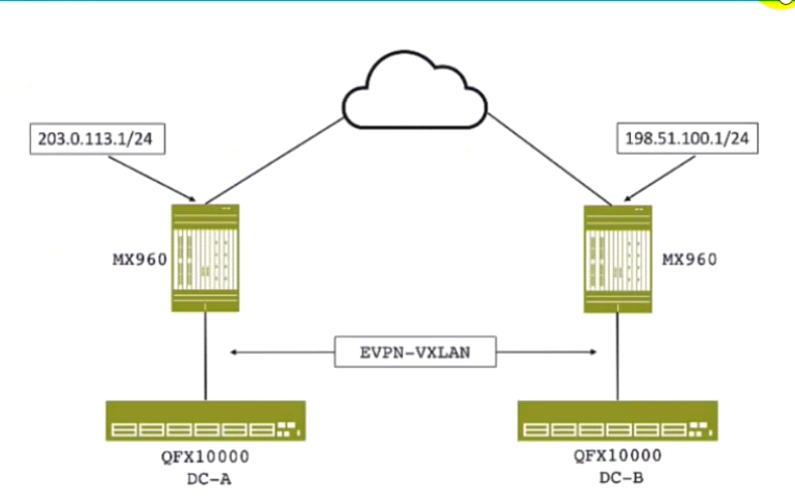
You are designing a Data Center Interconnect to transport VXLAN traffic between DC-A and DC-B
Which two technologies will allow the MX Series routers to transport the VXLAN packets over the WAN, as shown in the exhibit? (Choose two)
Answer : A, D
According to Juniper Networks, what are two recommendations for implementing data center security? (Choose two )
Answer : B, C