Juniper Security, Specialist JN0-335 Exam Questions
Exhibit
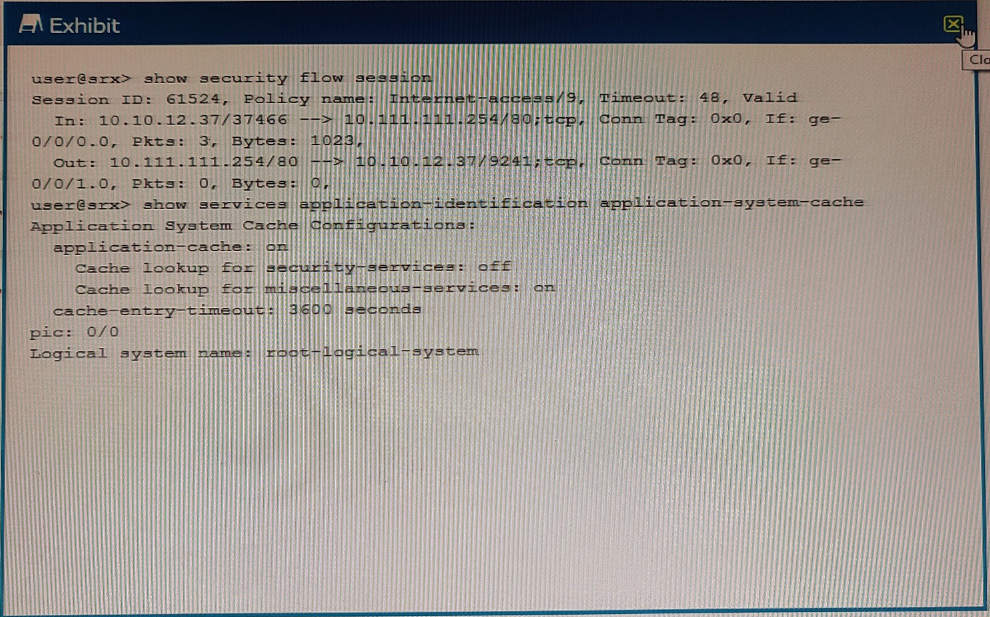
Referring to the exhibit which statement is true?
Answer : D
You want to manually failover the primary Routing Engine in an SRX Series high availability cluster pair.
Which step is necessary to accomplish this task?
Answer : A
In order to manually failover the primary Routing Engine in an SRX Series high availability cluster pair, you must issue the command 'set chassis cluster disable reboot' on the primary node. This command will disable the cluster and then reboot the primary node, causing the secondary node to take over as the primary node. This is discussed in greater detail in the Juniper Security, Specialist (JNCIS-SEC) Study Guide (page 68).
Which two statements are true about application identification? (Choose two.)
Answer : A, D
Application identification is a feature that enables SRX Series devices to identify and classify network traffic based on application signatures or custom rules. Application identification can enhance security, visibility, and control over network applications. Two statements that are true about application identification are:
Application identification can identify nested applications that are within Layer 7: Nested applications are applications that run within another application protocol, such as HTTP or SSL. For example, Facebook or YouTube are nested applications within HTTP. Application identification can identify nested applications by inspecting the application payload and matching it against predefined or custom signatures.
Application signatures are not the same as IDP signatures: Application signatures are patterns of bytes or strings that uniquely identify an application protocol or a nested application. IDP signatures are patterns of bytes or strings that indicate an attack or an exploit against a vulnerability. Application signatures are used for application identification and classification, while IDP signatures are used for intrusion detection and prevention.
Your company is using the Juniper ATP Cloud free model. The current inspection profile is set at 10 MB You are asked to configure ATP Cloud so that executable files up to 30 MB can be scanned while at the same time minimizing the change in scan time for other file types.
Which configuration should you use in this scenario?
Answer : D
In this scenario, you should use the ATP Cloud Ul to create a custom profile and update the scan limit for executable files to 30 MB. This will ensure that executable files up to 30 MB can be scanned, while at the same time minimizing the change in scan time for other file types. To do this, log in to the ATP Cloud Ul and go to the Profiles tab. Click the Create button to create a new profile, and then adjust the scan limits for executable files to 30 MB. Once you have saved the custom profile, you can apply it to the desired systems and the new scan limit will be in effect.
Exhibit
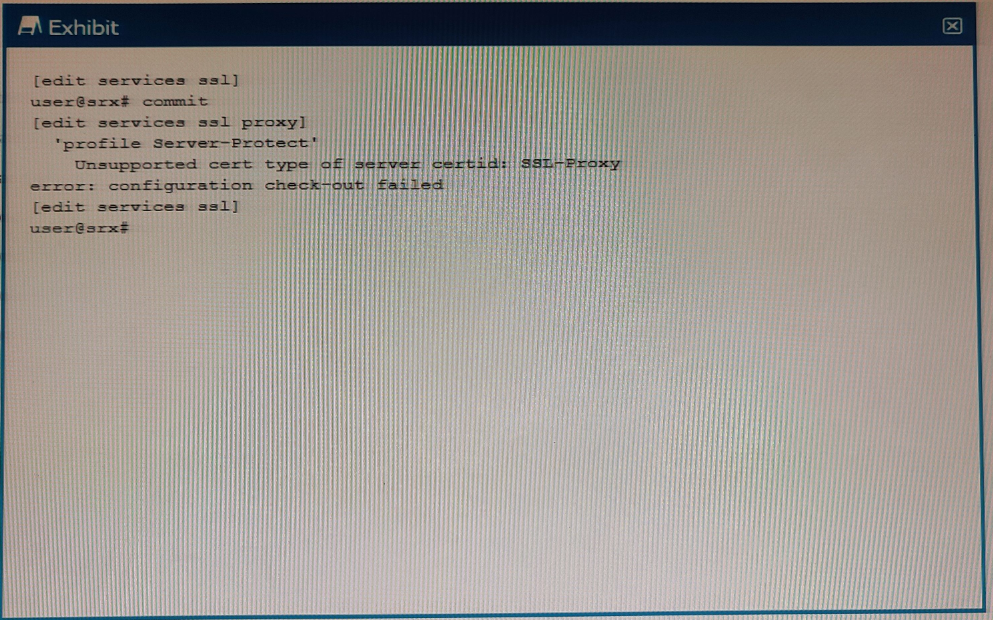
When trying to set up a server protection SSL proxy, you receive the error shown. What are two reasons for this error? (Choose two.)
You want to use IPS signatures to monitor traffic.
Which module in the AppSecure suite will help in this task?
Answer : C
The AppFW module in the AppSecure suite provides IPS signatures that can be used to monitor traffic and detect malicious activities. AppFW also provides other security controls such as Web application firewall, URL filtering, and application-level visibility.
Exhibit
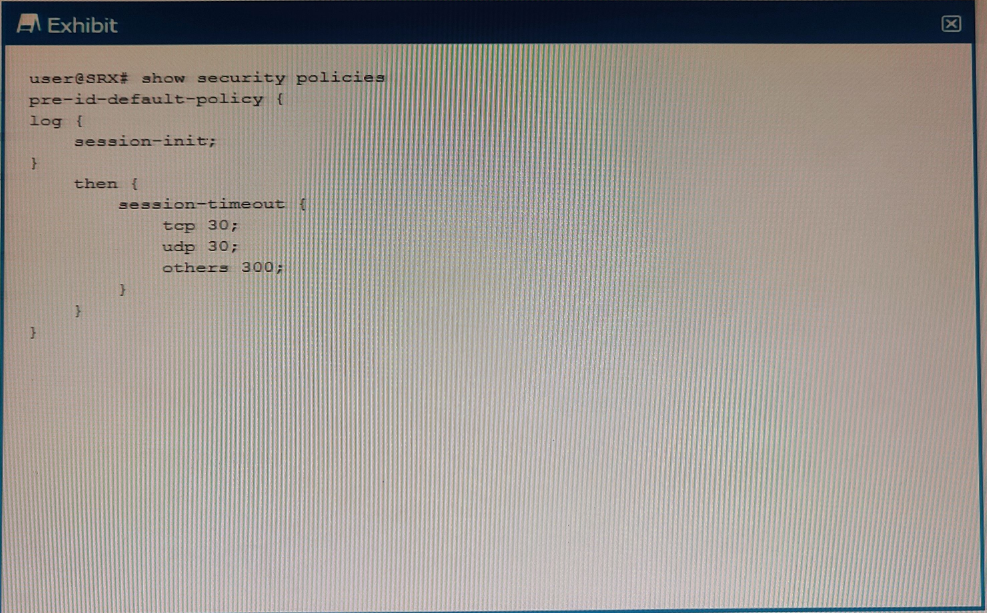
Which two statements are correct about the configuration shown in the exhibit? (Choose two.)
Answer : B, C
The configuration shown in the exhibit is for a Juniper SRX Series firewall. The session-init parameter is used to control how the firewall processes unknown traffic flows. With the session-init parameter set to 300, any traffic flows that the firewall does not recognize will be dropped after 300 milliseconds. Additionally, every session that enters the device, whether it is known or unknown, will generate an event, which can be used for logging and troubleshooting purposes. The session-lose parameter is used to control how the firewall handles established sessions that are terminated.