Juniper Security, Specialist JN0-335 Exam Questions
You want to permit access to an application but block application sub-Which two security policy features provide this capability? (Choose two.)
Answer : A, B
The two security policy features that provide the capability to permit access to an application but block its sub-applications are URL filtering and micro application detection. URL filtering allows you to create policies that permit or block access to certain websites or webpages based on URL patterns. Micro application detection is a more sophisticated approach that can identify and block specific applications, even if they are embedded within other applications or websites. According to the Juniper Networks Certified Internet Specialist (JNCIS-SEC) Study Guide[1], ''micro application detection is the most accurate way to detect and control applications.'' Content filtering and APPID are more general approaches and are not as effective in providing the level of granularity needed to block sub-applications.
Exhibit
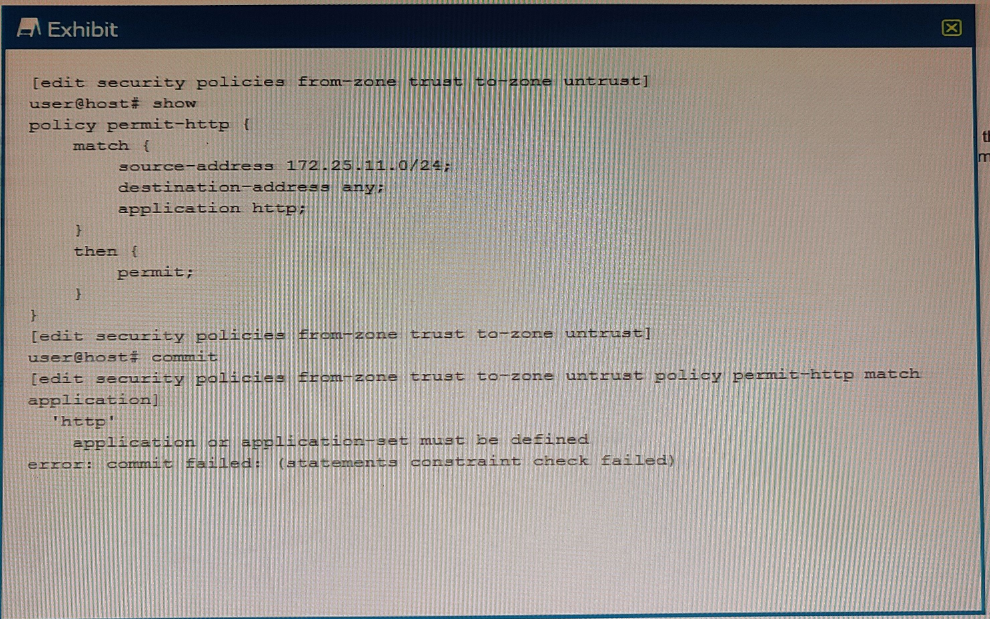
You are trying to create a security policy on your SRX Series device that permits HTTP traffic from your private 172 25.11.0/24 subnet to the Internet You create a policy named permit-http between the trust and untrust zones that permits HTTP traffic. When you issue a commit command to apply the configuration changes, the commit fails with the error shown in the exhibit.
Which two actions would correct the error? (Choose two.)
Answer : C, D
The error message indicates that the Junos-http application is not defined, so you need to either create a custom application or modify the security policy to use the built-in Junos-http application. Doing either of these will allow you to successfully commit the configuration.
You want to deploy a virtualized SRX in your environment.
In this scenario, why would you use a vSRX instead of a cSRX? (Choose two.)
Answer : A, C
The vSRX supports both Layer 2 and Layer 3 configurations, while the cSRX is limited to Layer 3 configurations. Additionally, the vSRX has faster boot times, which is advantageous in certain scenarios. The vSRX and cSRX both provide NAT, IPS, and UTM services.
Which method does the loT Security feature use to identify traffic sourced from IoT devices?
Answer : D
The metadata is used to identify the type of device, its associated activities and its threat profile. This information is used to determine the appropriate security policy for the device. For more information on loT Security, please refer to the Juniper Security, Specialist (JNCIS-SEC) study guide.
Which statement regarding Juniper Identity Management Service (JIMS) domain PC probes is true?
Answer : B
Juniper Identity Management Service (JIMS) domain PC probes are used to map usernames to IP addresses in the domain security event log. This allows for the SRX Series device to verify authentication table information, such as group membership. The probes are triggered whenever a username to IP address mapping is not found in the domain security event log. By default, the probes are executed at 60-minute intervals.
Which two statements about SRX chassis clustering are correct? (Choose two.)
Answer : A, D
SRX chassis clustering supports active/passive and active/active for the data plane. In an active/active configuration, both cluster members process and forward traffic, which increases throughput and provides redundancy. For the control plane, SRX chassis clustering supports active/active, meaning that both cluster members can process and forward control traffic, providing redundancy and improved scalability
Which two statements are correct about AppTrack? (Choose two.)
Answer : A, C
AppTrack is a feature that allows you to monitor and analyze the application traffic on your SRX Series device. It can be configured for any defined logical system, which is a virtual router or switch within a physical device. AppTrack collects statistics such as bytes, packets, and duration for each application flow and displays them in reports or logs. AppTrack does not identify or block malicious traffic, that is the function of AppSecure or IDP/IPS.Reference:=JNCIS-SEC Certification,Open Learning - Security, Specialist (JNCIS-SEC),Application Security Theory