Juniper Security, Professional JN0-636 JNCIP-SEC Exam Questions
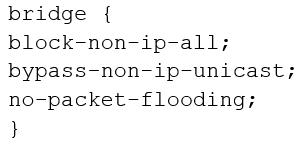
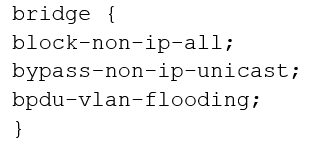
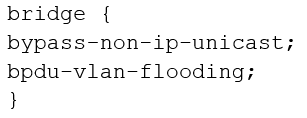
You are configuring transparent mode on an SRX Series device. You must permit IP-based traffic only, and BPDUs must be restricted to the VLANs from which they originate.
Which configuration accomplishes these objectives?
A)
B)
C)
D)
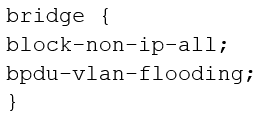
Answer : D
https://www.juniper.net/documentation/us/en/software/junos/multicast-l2/topics/ref/statement/family-ethernet-switching-edit-interfaces-qfx-series.html#statement-name-statement__d26608e73
Refer to the Exhibit.
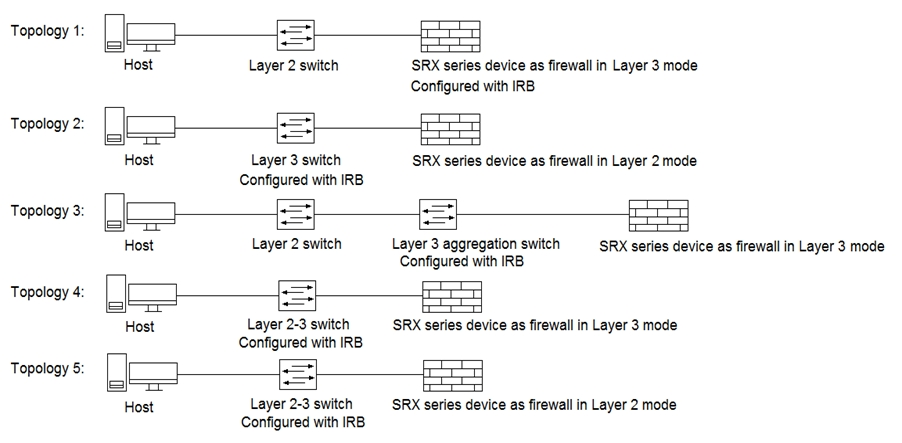
Referring to the exhibit, which three topologies are supported by Policy Enforcer? (Choose three.)
Answer : A, D, E
You opened a support ticket with JTAC for your Juniper ATP appliance. JTAC asks you to set up access to the device
using the reverse SSH connection.Which three setting must be configured to satisfy this request? (Choose three.)
Answer : C, D, E
https://kb.juniper.net/InfoCenter/index?page=content&id=TN326&cat=&actp=LIST&showDraft=false
Your company uses non-Juniper firewalls and you are asked to provide a Juniper solution for zero-day malware protection. Which solution would work in this scenario?
Answer : A
Juniper ATP Cloud provides zero-day malware protection for non-Juniper firewalls. It's a cloud-based service that analyzes files and network traffic to detect and prevent known and unknown (zero-day) threats. It uses a combination of static and dynamic analysis techniques, as well as machine learning, to detect and block malicious files, even if they are not known to traditional anti-virus software. It also provides real-time visibility and detailed forensics for incident response and remediation.
In Juniper ATP Cloud, what are two different actions available in a threat prevention policy to deal with an infected host? (Choose two.)
Answer : B, D
In Juniper ATP Cloud, a threat prevention policy allows you to define how the system should handle an infected host. Two of the available actions are:
Close the connection: This action will close the connection between the infected host and the destination to which it is trying to connect. This will prevent the host from communicating with the destination and will stop any malicious activity.
Quarantine the host: This action will isolate the infected host from the network by placing it in a quarantine VLAN. This will prevent the host from communicating with other devices on the network, which will prevent it from spreading malware or exfiltrating data.
Sending a custom message is used to notify the user and administrator of the action taken. Drop the connection silently is not an action available in Juniper ATP Cloud.
According to the Juniper documentation, the threat prevention policy in Juniper ATP Cloud is a configuration that defines the actions and notifications for different threat levels of the traffic. The threat levels are based on the verdicts returned by Juniper ATP Cloud after analyzing the files, URLs, and domains.The threat levels range from 1 to 10, where 1 is the lowest and 10 is the highest1.
The threat prevention policy allows the user to specify different actions for different threat levels. The actions can be applied to the traffic or to the infected host. The actions available for the traffic are:
Permit: Allows the traffic to pass through the SRX Series device without any interruption.
Block: Blocks the traffic and sends a reset packet to the client and the server.
Drop: Drops the traffic silently without sending any reset packet.
Redirect: Redirects the traffic to a specified URL, such as a warning page or a sinkhole server.
The actions available for the infected host are:
None: Does not take any action on the infected host.
Quarantine: Quarantines the infected host by applying a firewall filter that blocks all outbound traffic from the host, except for the traffic to Juniper ATP Cloud or the specified redirect URL.
Custom: Executes a custom script on the SRX Series device to perform a user-defined action on the infected host, such as sending an email notification or triggering an external system.
Therefore, the two different actions available in a threat prevention policy to deal with an infected host are:
Block: This action will block the traffic from or to the infected host and send a reset packet to the client and the server. This will prevent the infected host from communicating with the malicious server or spreading the malware to other hosts.
Quarantine: This action will quarantine the infected host by blocking all outbound traffic from the host, except for the traffic to Juniper ATP Cloud or the redirect URL. This will isolate the infected host from the network and allow the user to remediate the infection.
The following actions are not available or incorrect:
Send a custom message: This is not an action available in the threat prevention policy. However, the user can use the custom action to execute a script that can send a custom message to the infected host or the administrator.
Drop the connection silently: This is an action available for the traffic, not for the infected host. It will drop the traffic without sending any reset packet, which may not be effective in stopping the infection or notifying the user.
You configured a chassis cluster for high availability on an SRX Series device and enrolled this HA cluster with the Juniper ATP Cloud. Which two statements are correct in this scenario? (Choose two.)
Answer : B, D
When enrolling your devices, you only need to enroll one node: The Juniper ATP Cloud automatically recognizes the HA configuration and applies the same license and configuration to both nodes of the cluster.
You must use the same license key on both cluster nodes: The HA cluster needs to share the same license key in order to be recognized as a single device by the Juniper ATP Cloud.
You must set up your HA cluster before enrolling your devices with Juniper ATP Cloud. And it is not necessary to use different license keys on both cluster nodes because the HA cluster shares the same license key.
The two statements that are correct in this scenario are:
When enrolling your devices, you only need to enroll one node. This is because the Juniper ATP Cloud service supports chassis cluster mode for SRX Series devices. When you enroll a chassis cluster, you only need to enroll the primary node of the cluster. The secondary node will be automatically enrolled and synchronized with the primary node. You do not need to enroll the secondary node separately or perform any additional configuration on it.
You must use the same license key on both cluster nodes. This is because the Juniper ATP Cloud service requires a license key to activate the service on the SRX Series devices. The license key is tied to the serial number of the device. When you enroll a chassis cluster, you must use the same license key on both nodes of the cluster. The license key must match the serial number of the primary node of the cluster. You cannot use different license keys on the cluster nodes.
Click the Exhibit button.
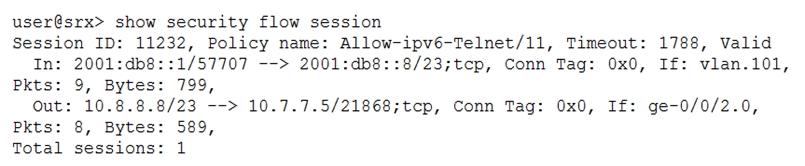
Which type of NAT is shown in the exhibit?
Answer : B