Juniper Security, Professional JN0-637 JNCIP-SEC Exam Questions
You have deployed automated threat mitigation using Security Director with Policy Enforcer, Juniper ATP Cloud, SRX Series devices, Forescout, and third-party switches.
In this scenario, which device is responsible for communicating directly to the third-party switches when infected hosts need to be blocked?
Answer : B
Policy Enforcer receives these policies and translates them into device-specific commands. It then communicates with the third-party switches (using protocols like SNMP, RADIUS, or vendor-specific APIs) to enforce those commands, such as blocking the infected hosts' MAC addresses or port access.
Why Policy Enforcer is the Right Choice:
Centralized Enforcement: Policy Enforcer acts as the central point of enforcement for Security Director policies, ensuring consistent security across the network.
Multi-Vendor Support: It can interact with a wide range of network devices, including switches from different vendors.
Automation: Policy Enforcer automates the policy enforcement process, enabling rapid response to threats.
Exhibit:
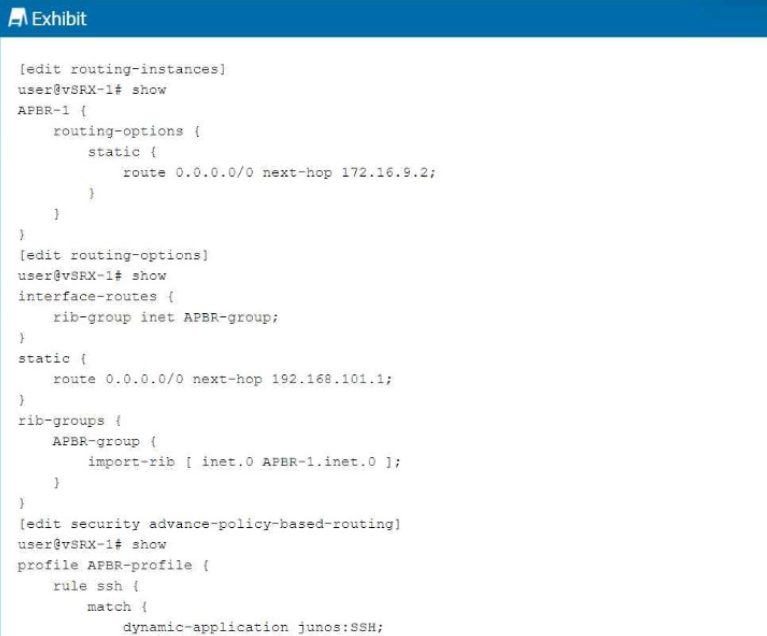
You are having problems configuring advanced policy-based routing.
What should you do to solve the problem?
Answer : B
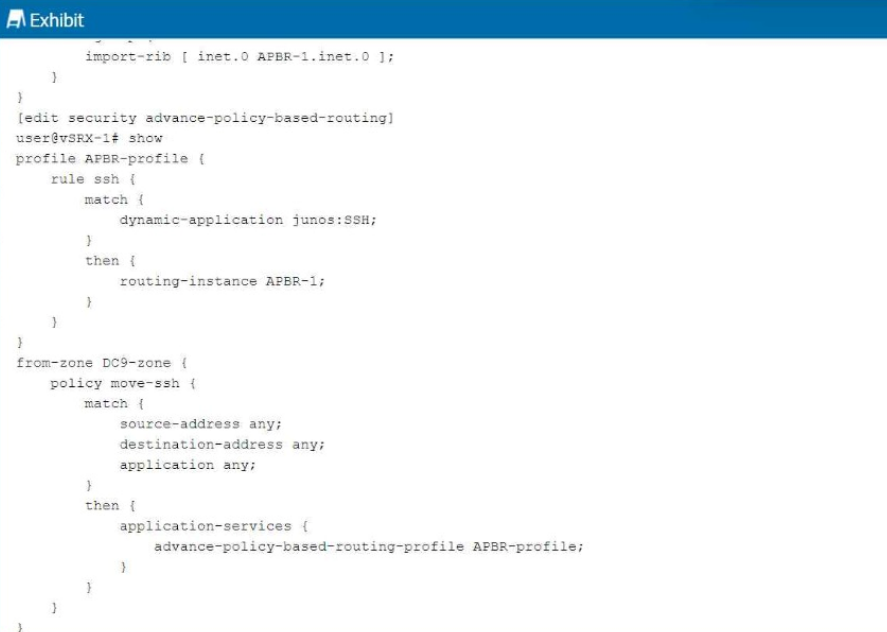
Click the Exhibit button.
Referring to the exhibit, which two statements are correct? (Choose two.)
Answer : C, D
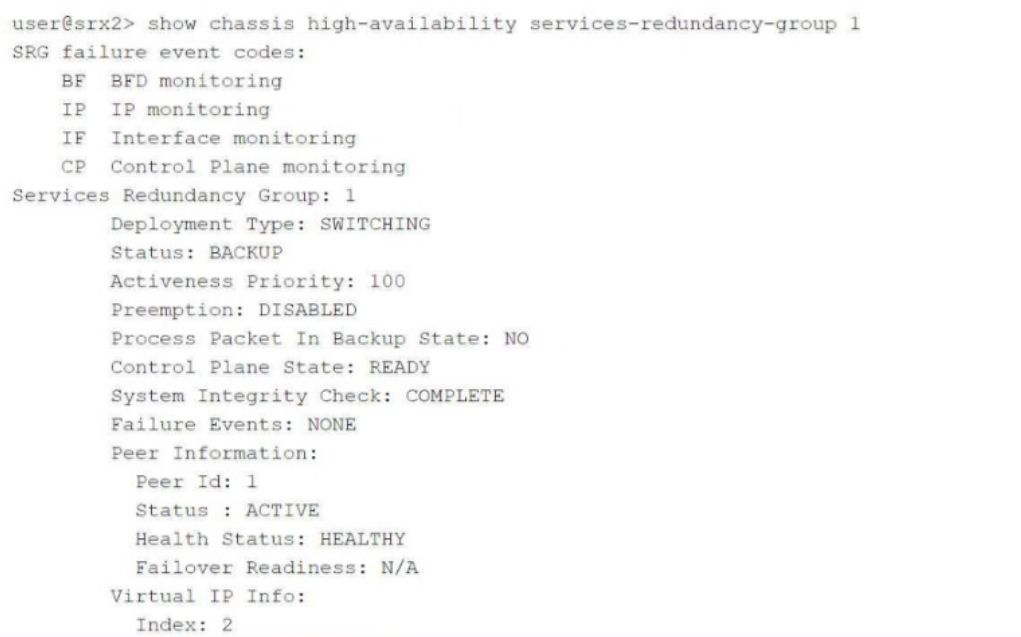
Exhibit:
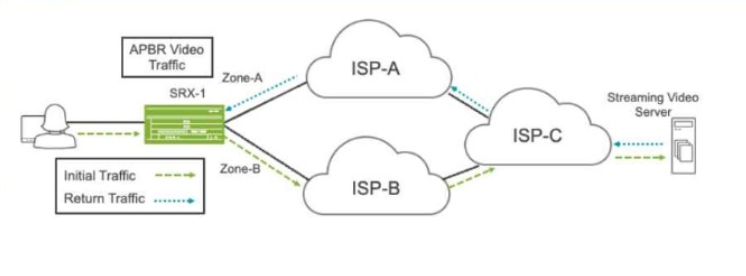
Referring to the exhibit, a default static route on SRX-1 sends all traffic to ISP-
Answer : D
Exhibit:
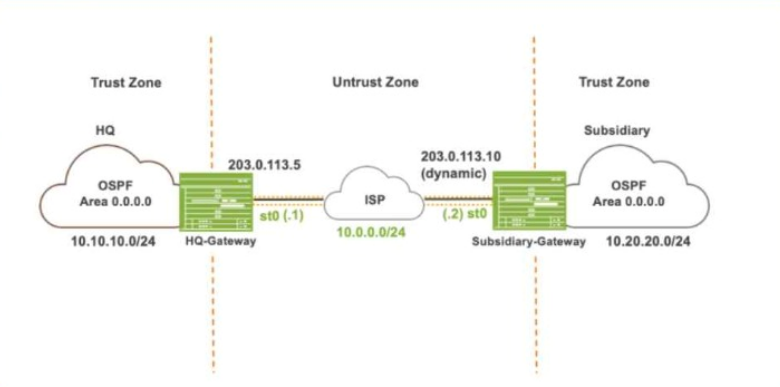
Referring to the exhibit, which IKE mode will be configured on the HQ-Gateway and Subsidiary-Gateway?
Answer : B
Which two statements are correct about mixed mode? (Choose two.)
Answer : B, C
Which encapsulation type must be configured on the lt-0/0/0 logical units for an interconnect
logical systems VPLS switch?
Answer : C