Juniper Enterprise Routing and Switching, Professional JN0-650 JNCIP-ENT Exam Questions
When configuring OSPF. what is the purpose of adding the secondary command to an OSPF interface?
Answer : B
In Junos OS, a physical or logical interface is typically associated with a single OSPF area. However, there are specific design requirements---such as migrating an interface from one area to another without downtime or creating specific transit topologies---where an interface needs to exist in two areas simultaneously.
Multi-area Adjacency (Option B): The secondary command under the OSPF interface hierarchy allows an interface to be part of a secondary area in addition to its primary area.
Protocol Behavior: When an interface is configured as secondary, the router sends and receives OSPF Hello packets for both the primary and secondary areas on that single link. This allows the router to form adjacencies with neighbors in both areas over the same physical connection.
Use Case: This is frequently used in hub-and-spoke topologies or during network restructuring to ensure reachability is maintained while changing area boundaries. It effectively allows a 'logical' split of the interface at the OSPF protocol level.
You have two multicast receivers connected to the same VLAN. You notice that the switch that they are connected to is forwarding multicast traffic out of all the ports in the same VLAN, instead of just the two ports for the connected multicast receivers
In this scenario, what would you configure to optimize multicast forwarding?
Answer : C
In a standard Layer 2 switch environment without specific multicast optimizations, multicast traffic is treated similarly to broadcast traffic and is flooded out of all ports within a VLAN (except the port where it was received). This is inefficient as it consumes unnecessary bandwidth on ports where no receivers are present.
To optimize this, IGMP Snooping is the standard solution.
How it works: The switch 'snoops' or monitors IGMP (Internet Group Management Protocol) messages between hosts and routers.
Result: When a receiver sends an IGMP Membership Report (Join) for a specific multicast group, the switch records which port that request came from. It then builds a Layer 2 multicast forwarding table so that traffic for that group is only forwarded to the specific ports that have active listeners.
Junos OS 24.4 Configuration: On modern Juniper switches, you enable this globally or per VLAN using the set protocols igmp-snooping vlan <vlan-name> command.
Option A (Promiscuous mode) is used for monitoring or specific security configurations (like Private VLANs) and would not limit multicast flooding. Option B (Spanning Tree) manages loop prevention and does not differentiate between traffic types for forwarding optimization. Option D (IRB interface) is used for Layer 3 routing between VLANs but does not inherently provide Layer 2 multicast optimization within a single VLAN.
Your router is discarding an EBGP route because the next hop is not directly connected. Which BGP configuration would you use to override this behavior?
Answer : B
In External BGP (EBGP), there is a default safety mechanism that requires the peer's next hop to be on a directly connected network.
TTL Constraint: By default, EBGP packets are sent with a Time-to-Live (TTL) value of 1. If the next hop is not directly connected (e.g., when peering via loopback interfaces or across a multi-hop path), the packet will expire before reaching the destination, causing the route to be discarded or the session to fail.
The Multihop Solution (Option B): To override this behavior, you must configure the multihop statement under the BGP neighbor or group hierarchy. This allows the BGP session to establish by increasing the TTL (typically to 64 or a user-defined value) and bypasses the 'directly connected' check.
Incorrect Options: Option A (accept-remote-nexthop) is used in internal BGP or specific routing-instance scenarios to resolve next hops that aren't in the local routing table, but it doesn't solve the EBGP TTL/direct-connection requirement. Option C (advertise-inactive) allows BGP to advertise routes that are not the best path in the routing table, which is irrelevant to next-hop reachability. Option D (multipath) is used for load-sharing across multiple paths.
You need to perform maintenance on one of your OSPF routers. You do not want the other OSPF routers on the network to forward traffic to this router dunng the maintenance window
Which OSPF configuration parameter would you implement to accomplish this task?
Answer : B
For maintenance scenarios where a router must remain operational but should not be used as a transit path for OSPF traffic, Junos OS uses the overload functionality.
OSPF Overload (Option B): When you enable overload under protocols ospf, the router advertises its own Link-State Advertisements (LSAs) with a maximum metric (65535) for all of its transit links.
Traffic Diversion: Because OSPF uses the Shortest Path First (SPF) algorithm to find the lowest-cost path, other routers in the network will see the overloaded router as an extremely high-cost path. They will calculate alternate routes, effectively moving transit traffic off the router while still allowing management traffic directed to the router's own interfaces.
Timeout Options: You can configure this to be permanent or set a timeout so that the router automatically resumes normal metric advertisements after a set period.
Your existing enterprise network uses OSPFv3 on Juniper devices. You need to extend the networking into a new building, and it needs to be in its own OSPF are
a. Your team is debating about making the area a stub
Which two statements are correct in this scenario? (Choose two.)
Answer : C, D
OSPF stub areas are used to reduce the size of the Link-State Database (LSDB) in routers with limited resources by restricting the flooding of external routes.
Virtual Links (Option C): According to OSPF standards (both v2 and v3), virtual links cannot pass through stub areas. A virtual link must transit a 'transit area,' which must be a standard (non-stub) area with a full routing table.
Totally Stubby Areas (Option D): A stub area (which blocks Type 5 External LSAs) can be further restricted into a totally stubby area. In Junos OS, this is done by adding the no-summaries statement to the stub configuration. This blocks both Type 5 and Type 3 (Inter-area) LSAs, replacing them with a single default route.
Incorrect Statements: Option A is incorrect because standard stub areas cannot contain an ASBR; only Not-So-Stubby Areas (NSSA) allow for an ASBR. Option B is incorrect because an area is either a Stub or an NSSA; they are mutually exclusive configurations for the same area.
You have deployed 802.1X with server fail fallback enabled on an EX Series switch and specified the vlan-name feature for all access ports. The RADIUS server is unavailable.
Which two statements are correct in this scenario? (Choose two )
Answer : B, D
When 802.1X server fail fallback is enabled with the vlan-name feature, the switch provides a specific survival mechanism for both existing and new sessions when the RADIUS server becomes unreachable.
Existing Clients (Statement B): Clients that have already successfully authenticated are unaffected by the server's unavailability in the short term. They maintain their current network access until their specific re-authentication timer expires. Only then will the switch attempt to contact the server again and trigger the fallback action if the server remains down.
New Clients (Statement D): For any new device attempting to connect while the RADIUS server is down, the switch cannot perform a standard authentication. Under the vlan-name fallback configuration, these new clients are automatically placed into the specified fallback VLAN and granted access based on the local policy defined for that VLAN.
Why others are incorrect: Statement A is incorrect because disconnecting active users would cause unnecessary service disruption. Statement C is incorrect because new clients cannot 'request' a VLAN during the 802.1X handshake; the switch assigns it based on the fallback configuration.
Exhibit.
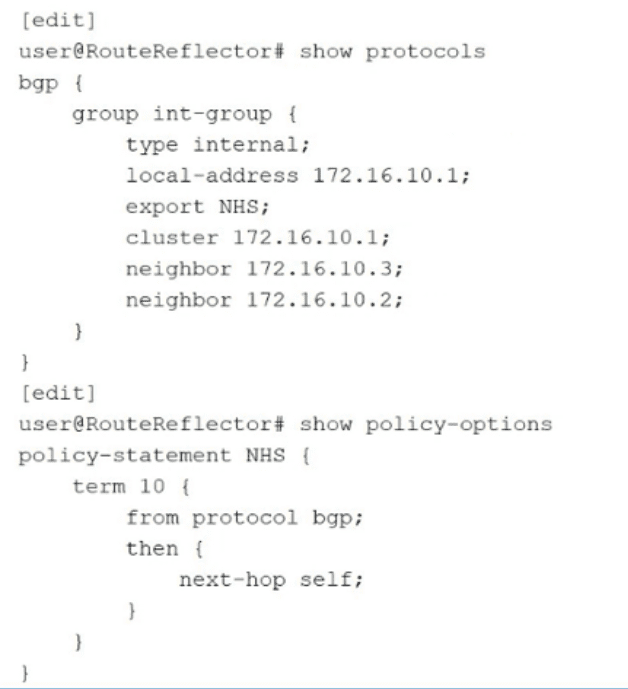
You have determined that traffic in your network is being routed through your route reflector instead of using the optimal path. Referring to the exhibit, what are two configuration changes on the route reflector that would solve the problem? (Choose two.)
Answer : C, D
The exhibit shows a BGP Route Reflector (RR) configuration where an export policy named NHS (Next-Hop Self) is applied to the internal BGP group int-group. The policy NHS sets the next-hop self attribute for BGP routes.
The Problem (Traffic Tromboning): In a standard BGP Route Reflector design, the RR should reflect routes without modifying the BGP next-hop attribute. By applying a next-hop self policy on the export to clients, the RR tells all its clients that it is the exit point for those routes. Consequently, all data plane traffic is sent to the RR first before being forwarded to the actual destination, rather than following the optimal direct path between clients. This is known as 'traffic tromboning' or suboptimal routing.
The Solution (Option C): The most direct way to fix this is to delete the export policy that is forcing the next-hop to be the RR. By deleting protocols bgp group int-group export NHS, the RR will resume standard behavior and reflect the original next-hop received from the route source, allowing clients to route traffic directly to the correct destination.
The Refined Solution (Option D): If you must keep the NHS policy (perhaps for routes learned from external peers), you should ensure it only applies to those specific routes. By adding from route-type internal to the policy term and then potentially changing the logic (or simply narrowing the scope), you can prevent the RR from incorrectly applying next-hop self to internal routes that it is merely reflecting. In the context of this specific problem, Option D combined with a change in the policy's action or scope helps ensure reflected internal routes maintain their original, optimal next-hops.
Option A is incorrect because setting next-hop self for external routes is common practice, but it doesn't solve the problem of internal reflected routes being diverted to the RR.
Option B is incorrect because applying this as an import policy would change how the RR itself sees the routes, but it wouldn't fix the attributes being sent out to the clients in the reflection process.