Logical Operations Certified CyberSec First Responder CFR-210 CFR Exam Questions
A company website was hacked via the SQL query below:
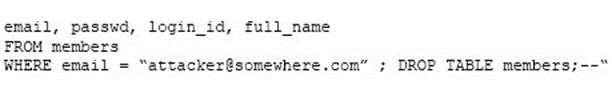
Which of the following did the hackers perform?
Answer : D
During the course of an investigation, an incident responder discovers illegal material on a user's hard drive. Which of the following is the incident responder's MOST important next step?
Answer : A
Log review shows that large amounts of data are being sent to an IP address unassociated with the company. Which of the following migration techniques should be implemented?
Answer : A
A Windows system user reports seeing a command prompt window pop up briefly during each login. In which of the following locations would an incident responder check to explain this activity?
Answer : C
Click the exhibit button. After reviewing captured network traffic logs, a security auditor suspects a violation of the organization's computer use policy. Which of the following is the likely indicator of the violation?
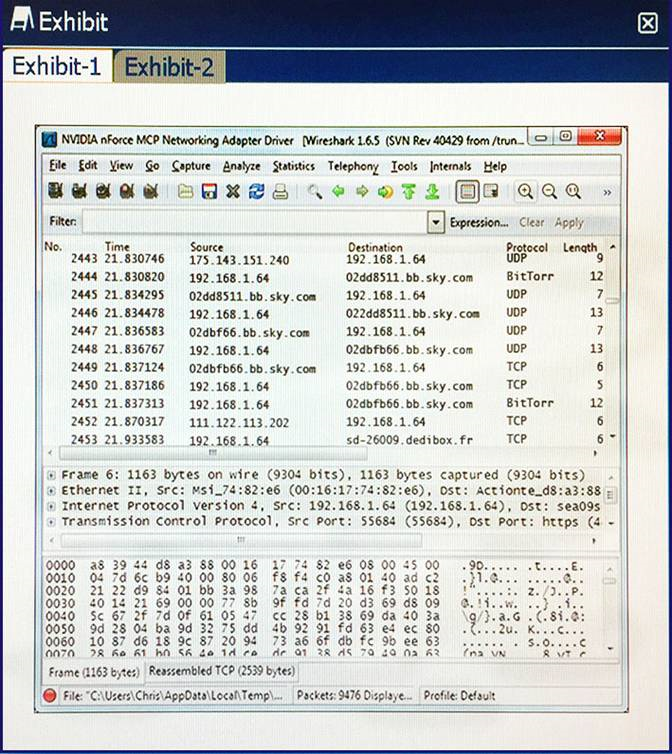
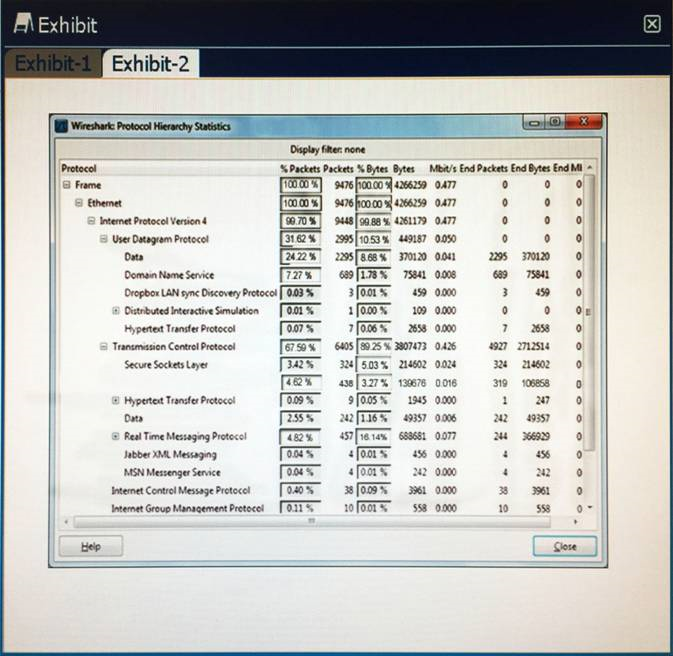
Answer : A
Which of the following are reasons that a hacker would execute a DoS or a DDoS attack? (Choose two.)
Answer : A, B
A SOC analyst has been tasked with checking all files in every employee home directory for any mention of a new product code named PitViper. Which of the following commands will return all requested data?
Answer : A