Microsoft Azure Administrator AZ-104 Exam Questions
You have an Azure subscription that contains two virtual machines named VM1 and VM2
You create an Azure load balancer.
You plan to create a load balancing rule that will load balance HTTPS traffic between VM1 and VM2.
Which two additional load balance resources should you create before you can create the load balancing rule? Each correct answer presents part of the solution
MOTL Each correct selection 5 worth one point.
Answer : A, C
To create a load balancing rule that will load balance HTTPS traffic between VM1 and VM2, you need to create two additional load balance resources: a frontend IP address and a health probe.
A frontend IP address is the IP address that the clients use to access the load balancer. It can be either public or private, depending on the type of load balancer.A frontend IP address is required for any load balancing rule1.
A health probe is used to monitor the health and availability of the backend instances. It can be either TCP, HTTP, or HTTPS, depending on the protocol of the load balancing rule.A health probe is required for any load balancing rule1.
A backend pool is a group of backend instances that receive the traffic from the load balancer. You already have a backend pool that contains VM1 and VM2, so you don't need to create another one.
An inbound NAT rule is used to forward traffic from a specific port on the frontend IP address to a specific port on a backend instance.It's not required for a load balancing rule, but it can be used to access individual instances for troubleshooting or maintenance purposes1.
A virtual network is a logical isolation of Azure resources within a region.It's not a load balance resource, but it's required for creating an internal load balancer or connecting virtual machines to a load balancer2.
You need to ensure that you can grant Group4 Azure RBAC read-only permissions to all the A2ure file shares. What should you do?
Answer : A
Azure role-based access control (Azure RBAC) for Azure file shares requires identity-based authentication integration. According to the Microsoft Azure Administrator documentation, this feature is only supported for StorageV2 (general purpose v2) and FileStorage account types.
In this scenario:
You are required to grant Group4 read-only access using Azure RBAC on Azure file shares.
The technical requirement specifies:
''Whenever possible, grant Group4 Azure RBAC read-only permissions to the Azure file shares.''
From the case study data:
Storage Account
Kind
Identity-based Access
storage1
Storage (general purpose v1)
Azure AD DS
storage2
StorageV2
Disabled
storage3
BlobStorage
N/A
storage4
FileStorage
Azure AD DS
The Storage (general purpose v1) type (storage1) does not support Azure AD or Azure RBAC integration for file shares. Microsoft documentation clearly states that ''StorageV1 accounts must be upgraded to StorageV2 to support Azure AD authentication and RBAC role assignments.''
Meanwhile, FileStorage (storage4) already supports Azure AD Domain Services (Azure AD DS) and RBAC role assignment; hence no further modification is required there. However, to make storage1 compatible, it must be converted from StorageV1 to StorageV2.
Once converted to StorageV2, you can then:
Enable identity-based access for Azure file shares.
Assign Azure RBAC roles (e.g., Storage File Data Reader) to Group4.
Microsoft-Documented Requirements Summary:
Supported Account Types: StorageV2 or FileStorage
Unsupported: StorageV1 and BlobStorage
Required RBAC Roles for Read-Only Access:
Storage File Data Reader (or custom read-only role)
Thus, to meet the organization's requirement to provide Azure RBAC read-only permissions, you must change the account type of storage1 to StorageV2, ensuring both storage1 and storage4 can be managed with Azure RBAC.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft Entra tenant named Adatum.com and an Azure Subscription named Subscription1. Adatum.com contains a group named Developers. Subscription1 contains a resource group named Dev.
You need to provide the Developers group with the ability to create Azure Logic Apps in the Dev resource group.
Solution: On Subscription1, you assign the DevTest Labs User role to the Developers group.
Does this meet the goal?
Answer : B
The DevTest Labs User role is a built-in Azure role designed specifically to support operations within Azure DevTest Labs. According to the Microsoft Azure Administrator documentation on built-in roles, this role permits users to connect to, start, stop, restart, and use virtual machines inside a DevTest Lab, but it does not grant permissions to create or manage Azure resources outside of DevTest Labs, such as Azure Logic Apps.
In this scenario, the requirement is to allow the Developers group to create Azure Logic Apps in the Dev resource group. Azure Logic Apps are managed through the Microsoft.Logic resource provider and require permissions such as Microsoft.Logic/workflows/write. These permissions are included in roles like Logic App Contributor or the more general Contributor role at the resource group scope.
The DevTest Labs User role does not include permissions to deploy or manage Logic Apps, even when assigned at the subscription level. Therefore, assigning this role does not meet the stated goal. Microsoft documentation explicitly states that DevTest Labs User is limited to DevTest Lab resources and cannot be used as a general deployment role.
Final Answer: B. No
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You need to ensure that an Azure Active Directory (Azure AD) user named Admin1 is assigned the required role to enable Traffic Analytics for an Azure subscription.
Solution: You assign the Traffic Manager Contributor role at the subscription level to Admin1
Answer : B
The Traffic Manager Contributor role is not related to Traffic Analytics. Traffic Manager is a service that provides DNS-based load balancing and traffic routing across different regions and endpoints.Traffic Manager Contributor is a role that allows you to create and manage Traffic Manager profiles, endpoints, and geographies1.
Traffic Analytics is a service that provides visibility into user and application activity in your cloud networks. Traffic Analytics analyzes Azure Network Watcher network security group (NSG) flow logs to provide insights into traffic flow in your Azure cloud.With Traffic Analytics, you can visualize network activity, identify hot spots, secure your network, optimize your network deployment, and pinpoint network misconfigurations2.
To enable Traffic Analytics for an Azure subscription, you need to have a role that grants you the following permissions at the subscription level:
Microsoft.Network/applicationGateways/read
Microsoft.Network/connections/read
Microsoft.Network/loadBalancers/read
Microsoft.Network/localNetworkGateways/read
Microsoft.Network/networkInterfaces/read
Microsoft.Network/networkSecurityGroups/read
Microsoft.Network/publicIPAddresses/read
Microsoft.Network/routeTables/read
Microsoft.Network/virtualNetworkGateways/read
Microsoft.Network/virtualNetworks/read
Microsoft.OperationalInsights/workspaces/*
Some of the built-in roles that have these permissions are Owner, Contributor, or Network Contributor3. However, these roles also grant other permissions that may not be necessary or desirable for enabling Traffic Analytics.Therefore, the best practice is to use the principle of least privilege and create a custom role that only has the required permissions for enabling Traffic Analytics4.
Therefore, to meet the goal of ensuring that an Azure AD user named Admin1 is assigned the required role to enable Traffic Analytics for an Azure subscription, you should create a custom role with the required permissions and assign it to Admin1 at the subscription level.
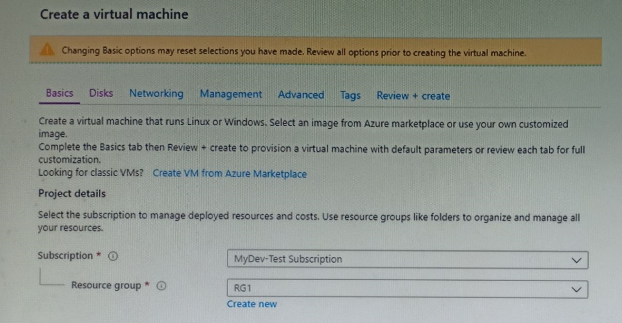
You plan to create an Azure virtual machine named VM1 that will be configured as shown in the following exhibit.
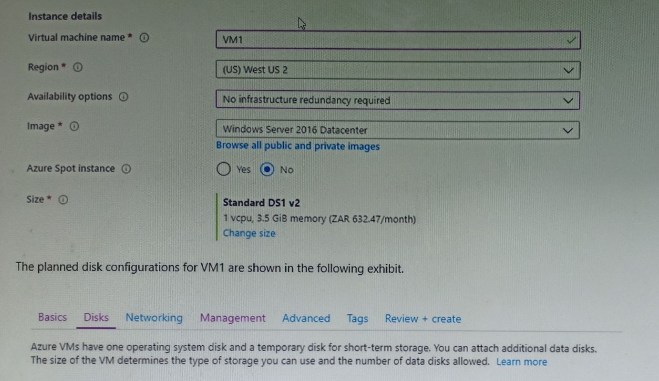
The planned disk configurations for VM1 are shown in the following exhibit.
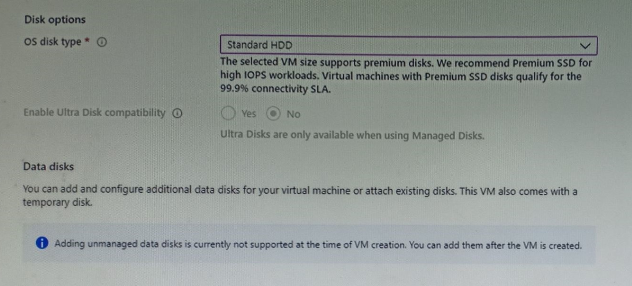
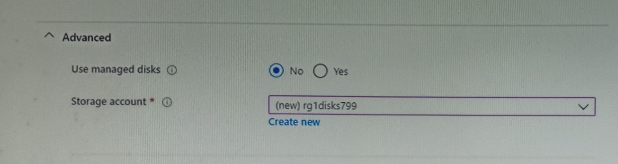
You need to ensure that VM1 can be created in an Availability Zone.
Which two settings should you modify? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
Answer : A, B
https://docs.microsoft.com/en-us/azure/site-recovery/move-azure-vms-avset-azone https://docs.microsoft.com/en-us/azure/virtual-machines/windows/create-portal-availability-zone https://docs.microsoft.com/en-us/azure/virtual-machines/manage-availability https://docs.microsoft.com/en-us/azure/availability-zones/az-overview#availability-zones
You have an Azure virtual machine named VM1 that runs Windows Server. The VM was deployed using default drive settings. You sign in to VM1 as a user named User1 and perform the following actions:
* Create files on drive C.
* Create files on drive D.
* Modify the screen saver timeout.
* Change the desktop background.
You plan to redeploy VM1. Which changes will be lost after you redeploy VM1?
Answer : A
When an Azure virtual machine is redeployed, Azure moves the VM to a new physical host. During this process, the OS disk and any attached data disks are preserved, but the temporary disk is not. On Windows VMs deployed with default settings, drive D: is the temporary disk, backed by local storage on the host. Microsoft documentation states that the temporary disk is non-persistent and data on it can be lost during maintenance, redeploy, or deallocation events. Files created on drive C: reside on the OS disk, which is persistent and retained across redeployments. User profile and system settings such as screen saver timeout and desktop background are stored on the OS disk and therefore remain intact after redeploy. Consequently, the only change that will be lost is data written to drive D:.
You have an Azure Kubernetes Service (AKS) cluster named AKS1.
You need to configure cluster autoscaler for AKS1.
Which two tools should you use? Each correct answer presents a complete solution,
NOTE: Each correct selection is worth one point
Answer : B, C
AKS clusters can scale in one of two ways: - The cluster autoscaler watches for pods that can't be scheduled on nodes because of resource constraints. The cluster then automatically increases the number of nodes. - The horizontal pod autoscaler uses the Metrics Server in a Kubernetes cluster to monitor the resource demand of pods. If an application needs more resources, the number of pods is automatically increased to meet the demand. Reference: https://docs.microsoft.com/en-us/azure/aks/cluster-autoscaler