Microsoft Troubleshooting Microsoft Azure Connectivity AZ-720 Exam Questions
You need to troubleshoot the CosmosDB1 issues from the on-premises environment. What should you use?
Answer : C
This tool helps you troubleshoot network connectivity issues from a virtual machine to a given endpoint.It tests for reachability from the virtual machine to the endpoint and provides information about why a connection fails1. In this case, you can use this tool to troubleshoot the connectivity issues from the on-premises environment to CosmosDB1.
A company enables just-in-time (JIT) virtual machine (VM) access in Azure.
An administrator observes a list of VMs on the Unsupported tab of the JIT VM access page in the Microsoft Defender for Cloud portal.
You need to determine why some VMs are not supported for JIT VM access.
What should you conclude?
Answer : B
JIT VM access is only supported for VMs that are deployed using the Azure Resource Manager (ARM) deployment model. VMs that are provisioned using the classic deployment model are not compatible with JIT VM access and will be displayed under the Unsupported tab of the JIT VM access page in the Microsoft Defender for Cloud portal.
You need to resolve the issue with VM10.
What should you do?
Answer : B
To resolve the issue with VM10, you need to remove the inbound security rule that has a priority of 100 in NSG10, which is blocking ICMP traffic from ASG1 to ASG10. The rule has a source of Any, a destination of VirtualNetwork, a protocol of ICMP, and an action of Deny. This means that any ICMP traffic from outside the VNet4 address space will be denied by NSG10, which is attached to subnet4. This prevents VM1 from pinging VM10 by using ICMP, as VM1 is in VNet1 and not in VNet4. By removing this rule, you can allow ICMP traffic from ASG1 to ASG10, as there is no other rule in NSG10 that explicitly denies it. Alternatively, you could also modify the rule to change the source to VirtualNetwork or the action to Allow, but removing the rule is simpler and more effective.
A company has an ExpressRoute gateway between their on-premises site and Azure. The ExpressRoute gateway is on a virtual network named VNet1. The company enables FastPath on the gateway. You associate a network security group (NSG) with all of the subnets.
Users report issues connecting to VM1 from the on-premises environment. VM1 is on a virtual network named VNet2. Virtual network peering is enabled between VNet1 and VNet2.
You create a flow log named FlowLog1 and enable it on the NSG associated with the gateway subnet.
You discover that FlowLog1 is not reporting outbound flow traffic.
You need to resolve the issue with FlowLog1.
What should you do?
Answer : A
According to1, flow logging using ExpressRoute Traffic Collector requires version 2 of flow logs. Version 1 of flow logs does not support ExpressRoute Traffic Collector. You can configure the version of flow logs when you enable them on a network security group (NSG).
A company migrates an on-premises Windows virtual machine (VM) to Azure. An administrator enables backups for the VM by using the Azure portal.
The company reports that the Azure VM backup job is failing.
You need to troubleshoot the issue.
Solution: Install the VM guest agent by using administrative permissions.
Does the solution meet the goal?
Answer : A
Yes, installing the VM guest agent by using administrative permissions could resolve the issue of the Azure VM backup job failing after enabling backups for the VM through the Azure portal. When backing up a virtual machine in Azure, it is necessary to install the VM guest agent to enable proper communication between the VM and the backup service. An administrative user account is required to install the agent.
Therefore, the solution mentioned in the question is correct and the answer is A. Yes.
Back up a virtual machine in Azure (Microsoft documentation)
You need to resolve the VM2 routing issue.
What should you do?
Answer : D
To resolve the VM2 routing issue, you should modify the IP configuration setting of the Azure network interface resource of VM2. This will ensure that VM2 can communicate with other resources in the virtual network.
Troubleshooting connectivity problems between Azure VMs involves several steps such as checking whether NIC is misconfigured, whether network traffic is blocked by NSG or UDR, whether network traffic is blocked by VM firewall, whether VM app or service is listening on the port and whether the problem is caused by SNAT1.
Fabrikam Inc. runs an online reservation service that allows agents to manage online registrations for various hotels, vacation rentals, and customers.
The company has on-premises infrastructure and services that are hosted in Azure. The on-premises infrastructure includes servers that run Active Directory Domain Services (AD DS). Azure services include virtual machines (VMs) that are in one subscription and the following environments: development, testing, and production. Each environment is located in a different virtual network (VNet).
The company has a perimeter network that supports connections to the internet. The perimeter network is also hosted in a separate VNet All of the VNets are
connected by using virtual network peering.
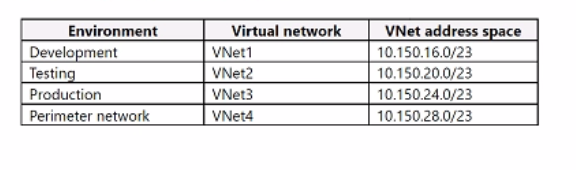
The company's subscription contains the following Azure virtual machines (VMs):
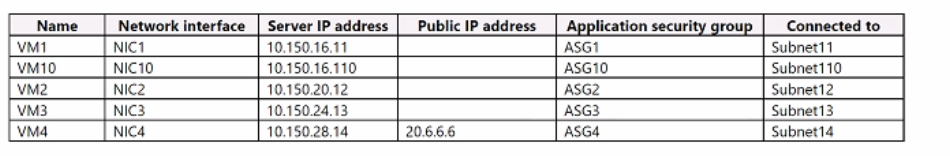
The Web Server (IIS) role is installed on VM4 The operating system firewall for each VM allows inbound ping requests.
The company's subscription includes the following network security groups (NSGs):
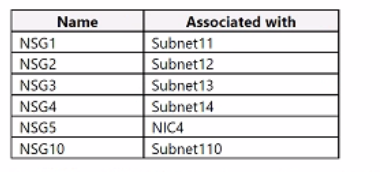
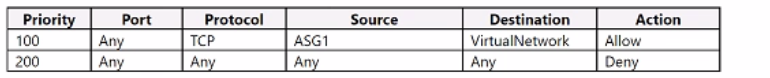
NSG1, NSG2. NSG3, and NSG5 use the default inbound security rules. NSG4. NSG5. and NSG10 use the default outbound security rules. NSG4 has the following inbound security rule:
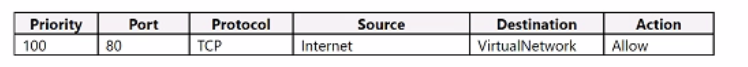
NSG10 has the following inbound security rules:
Network Policy Server (NPS) is installed on an on-premises server named SRV2. The NPS extension for Azure AD multi-factor authentication (MFA) is configured on the server as well.
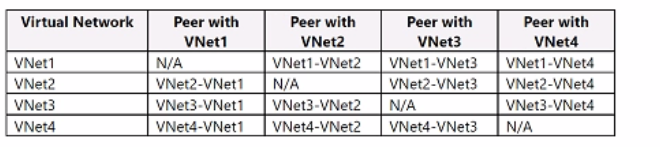
The virtual network peering connections are in the following table.
You provision a virtual network gateway named VNetGW in the perimeter network. The virtual network gateway uses SKU VpnGw1 and the public IP address 16.4.4.4 The virtual network gateway will provide:
* Network routing to customer data centers using site-to-site VPN connections.
* Network routing to Azure for the scheduling agents and sales employees using a point-to-site VPN connection.
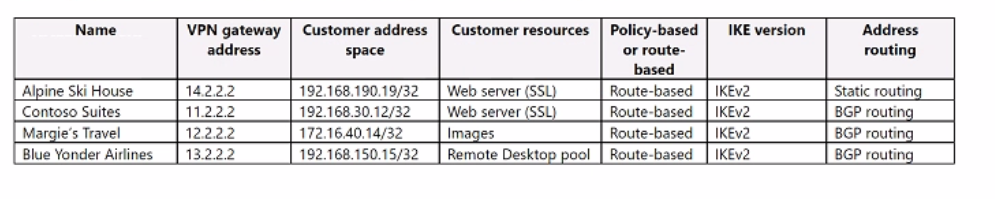
The company's site-to-site VPN connections with customers are shown in the following table.
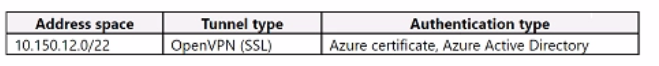
The point-to-site VPN is configured as shown in the following table;
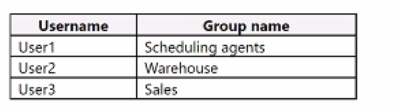
The company's user and group memberships are shown in the following table:
The scheduling agents, warehouse, and sales groups are members of the self-service password reset (SSPR) group named SSPR-group.
Azure AD Connect is installed on an on-premises server named SRV1. In addition;
* The server uses a pass-through authentication agent.
* The SSPR feature is enabled
* The SSPR feature is applied only to a group named SSPR-group
* The scheduling agents' internet connectivity must be blocked when connected to the point-to-site VPN.
* Sales employees must use the default VPN client on MacOS computers to connect to Azure.
* Azure AD Connect must synchronize all user accounts from AD DS to Azure AD.
* Pass-through authentication is required for all users.
* Azure AD multi-factor authentication (MFA) is requited for all users.
* All admin user accounts must be in an organizational unit (OU) named Admins.
A company has an Azure tenant. The company deploys an Azure firewall named FW1 to control access from an on-premises datacenter to an Azure virtual machine named VM1.
The company troubleshoots ICMP connectivity from the on-premises datacenter to VM1. You are unable to ping VM1 from an on-premises server.
You need to determine if ICMP connectivity to VM1 is allow on FW1.
What should you do?
Answer : C
According to Microsoft, the ICMP protocol is not permitted through the Azure load balancer. To test connectivity, Microsoft recommends that you do a port ping.While Ping.exe uses ICMP, you can use other tools, such as PSPing, Nmap, and telnet, to test connectivity to a specific TCP port1.