Microsoft Administering Windows Server Hybrid Core Infrastructure AZ-800 Exam Questions
You need to meet the technical requirements for User1. The solution must use the principle of least privilege.
What should you do?
Answer : D
n the Administering Windows Server Hybrid Core Infrastructure guidance for managing AD DS, Microsoft emphasizes using OU-level delegation to satisfy administrative needs while adhering to the principle of least privilege. The documentation explains that the Delegate Control wizard on an OU lets you grant a user or group only the specific permissions required for common tasks, including ''Modify the membership of a group''. This grants the write permission to the member attribute on group objects contained in that OU, without giving broader account-management rights across the domain.
By contrast, placing a user in Account Operators or Server Operators provides elevated, domain-wide capabilities far beyond what is required. Account Operators can create, delete, and modify many account types across the domain (except for protected admin accounts), which violates least-privilege for a task that only needs to change group membership in one OU. Server Operators is unrelated to group membership and is intended for server administration tasks. Creating a delegation at the domain root would similarly be excessive because it applies broadly to all containers and OUs.
Therefore, to meet the requirement ''Ensure that User1 can manage the membership of all the groups in Contoso\OU3,'' you should delegate control on OU3 and assign the built-in task ''Modify the membership of a group'' to User1, achieving the minimal permissions necessary.
You have an Active Directory Domain Services (AD DS) domain. The domain contains three servers named Server 1, Server2, and Server3 that run Windows Server.
You sign in to Server1 by using a domain account and start a remote PowerShell session to Server2. From the remote PowerShell session, you attempt to access a resource on Server3. but access to the resource is denied.
You need to ensure that your credentials are passed from Server1 to Server3. The solution must minimize administrative effort. What should you do?
Answer : A
In the Administering Windows Server Hybrid Core Infrastructure material under Windows Remote Management/PowerShell Remoting and authentication, Microsoft describes the classic ''second-hop'' issue: when you start a remote session to Server2 using Kerberos and then try to reach a resource on Server3, ''your delegated credentials are not forwarded by default.'' The guide explains that Kerberos ''does not allow delegation unless it is explicitly configured,'' and the recommended domain-based solution is Kerberos constrained delegation (KCD). With KCD you ''permit a specific computer account to delegate a user's Kerberos credentials only to explicitly listed services,'' for example allowing Server2 (the WinRM/HTTP endpoint you connect to) to delegate to CIFS on Server3 so file or other resource access succeeds during the second hop.
The docs contrast this with alternatives: CredSSP can work but ''is broader in exposure and requires enabling a less restrictive credential delegation mechanism,'' while JEA limits what commands can be run and does not solve credential delegation. Selective authentication applies to forest trusts, and Enforce user logon restrictions relates to KDC validation and is not a remedy for second-hop delegation. Because the requirement is to pass credentials from Server1 Server2 Server3 with minimal administrative touch and preserve security boundaries, configuring Kerberos constrained delegation on Server2's computer account for the target services on Server3 is the correct approach.
SIMULATION
Task 6
You need to enable nested visualization for a virtual machine named VM1 onSRV1.
Answer : A
TASK 6
Objective:
Enable nested virtualization for a VM (VM1) on SRV1.
Step-by-Step Guide: Enable Nested Virtualization
Step 1: Verify Requirements
Nested virtualization requires:
SRV1 to have a processor that supports Intel VT-x or AMD-V.
Hyper-V role installed on SRV1.
VM1 must be turned off.
Step 2: Open PowerShell on SRV1
Log in to SRV1 with an account that has administrative privileges.
Open PowerShell as Administrator.
Step 3: Enable Nested Virtualization
Run the following command:
Set-VMProcessor -VMName 'VM1' -ExposeVirtualizationExtensions $true
Step 4: Verify Nested Virtualization
To confirm the change, run:
Get-VMProcessor -VMName 'VM1' | Format-List ExposeVirtualizationExtensions
The output should show:
ExposeVirtualizationExtensions : True
Step 5: Configure Network Adapter (Optional for Nested VMs)
Nested virtualization requires MAC address spoofing for the VM network adapter.
Run:
Set-VMNetworkAdapter -VMName 'VM1' -MacAddressSpoofing On
Step 6: Start the VM
Use PowerShell:
Start-VM -Name 'VM1'
Or start the VM in Hyper-V Manager.
Additional Notes
Nested virtualization allows you to run Hyper-V within a VM.
Useful for lab/test environments (e.g., running nested Hyper-V hosts in a VM).
You have a server that runs Windows Server 2022 and has the network adapters shown in the following table.
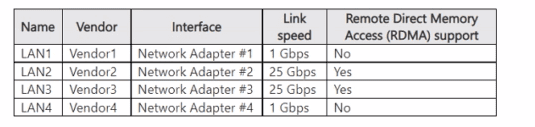
You need to configure NIC learning for LAN2 and LAN3. The solution must support Dynamic Virtual Machine Multi-Queue (d.VMMQ).
What should you use?
Answer : B
The networking section of the AZ-800 material specifies that Switch Embedded Teaming (SET) is the teaming technology for Hyper-V hosts introduced in Windows Server 2016 and enhanced in later versions. The guide highlights that SET ''integrates teaming into the Hyper-V virtual switch,'' and supports advanced offloads including RDMA, VMMQ/d.VMMQ, SR-IOV, and RSS when the NICs support them. Conversely, the legacy LBFO (Load Balancing/Failover) teaming is described as ''not supported with RDMA or VMMQ on Hyper-V hosts'' and is deprecated for Hyper-V scenarios. Static or LACP teaming modes refer to LBFO team modes and thus inherit those limitations. Because LAN2 and LAN3 are 25-Gbps adapters that support RDMA and the requirement explicitly calls for NIC learning with Dynamic VMMQ, the prescribed and supported solution is to create a SET team using those two adapters and bind it to the Hyper-V switch. The documentation emphasizes that SET ''enables RDMA with SMB Direct and Dynamic VMMQ on teamed NICs,'' meeting the performance and capability requirements.
Your network contains an Active Domain Services (AD DS) forest. The forest contains three domains. Each domain contains 10 domain controllers.
You plan to store a DNS zone in a custom active Directory partition.
You need to create the Active Directory partition for the zone. The partition replicate to only four of the domain controllers.
What should you use?
Answer : C
In the Windows Server hybrid administration guidance for DNS, Microsoft describes that DNS zones stored in Active Directory can use application directory partitions to customize replication scope beyond the default domain- or forest-wide options. The study materials state that ''custom application directory partitions allow DNS data to replicate only to the DNS servers that are explicitly enlisted in that partition.'' They further emphasize that while DNS Manager lets you pick among built-in scopes or select an existing application partition, ''creating a new application directory partition is performed with command-line tools (dnscmd) or Windows PowerShell.''
The documented procedure is: ''Use dnscmd /CreateDirectoryPartition <FQDN-of-partition> to create the custom partition, then dnscmd /EnlistDirectoryPartition on each DNS server that should host and replicate the data.'' Because you must have the partition replicate to only four of the domain controllers, you first create the partition, and then enlist only those four DNS servers. Tools such as Active Directory Sites and Services or Active Directory Administrative Center do not create DNS application directory partitions, and DNS Manager cannot create a new custom partition; it can only use an existing one. Therefore, the correct tool to meet the requirement is dnscmd.exe, after which you enlist just the selected four DNS servers into that partition.
You have an on premises Active Directory Domain Services (AD DS) domain that syncs with an Azure Active Directory (Azure AD) tenant. The domain contains two servers named Server1 and Server2.
A user named Admin1 is a member of the local Administrators group on Server1 and Server2.
You plan to manage Server1 and Server2 by using Azure Arc. Azure Arc objects will be added to a resource group named RG1.
You need to ensure that Admin1 can configure Server1 and Server2 to be managed by using Azure Arc.
What should you do first?
Answer : B
In the Administering Windows Server Hybrid Core Infrastructure content for Azure Arc--enabled servers, the onboarding script (interactive or service-principal based) requires that the identity used to connect a machine has the least-privilege built-in role at the intended scope. The guide states that for scripted or portal onboarding you should ''grant the Azure RBAC role Azure Connected Machine Onboarding at the subscription or resource-group scope to the identity that will run the connect process; this role includes only the permissions necessary to register and connect the server resource.'' It also notes that no hybrid Azure AD join is required just to onboard Arc, and that local admin on the target server is sufficient for installing the Connected Machine agent. Therefore, before Admin1 runs the onboarding script for Server1 and Server2 into RG1, you must first assign Admin1 the Azure Connected Machine Onboarding role at RG1. This satisfies least privilege and enables the script to create the Microsoft.HybridCompute/machines resource entries and related artifacts while avoiding broader roles like Contributor or Owner.
Your network contains a multi-site Active Directory Domain Services (AD DS) forest. Each Active Directory site is connected by using manually configured site links and automatically generated connections.
You need to minimize the convergence time for changes to Active Directory.
What should you do?
Answer : A
The Active Directory replication module explains that inter-site replication defaults to scheduled polling with a 180-minute interval and does not use change notifications. The guide notes: ''To reduce replication latency (convergence time) between sites, you can enable inter-site change notifications by setting the site link options attribute. When enabled, a change at one site triggers notifications to partners across the site link, initiating replication promptly rather than waiting for the next schedule.'' Adjusting site link cost influences topology selection by the KCC but ''does not change the frequency of replication.'' Similarly, editing the replication schedule can help, but even an 'always on' schedule retains the inter-site polling behavior unless change notification is enabled; the documented fastest method is enabling change notification via the options attribute on each site link. Creating site link bridges is intended for transitivity/topology and does not directly lower latency. Therefore, to minimize convergence time, modify the options attribute on each site link to enable inter-site change notifications.