Microsoft Identity and Access Administrator SC-300 Exam Questions
You have an Azure subscription that contains the users shown in the following table.
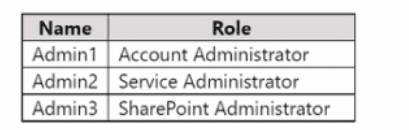
You need to implement Azure AD Privileged Identity Management (PIM).
Which users can use PIM to activate their role permissions?
Answer : D
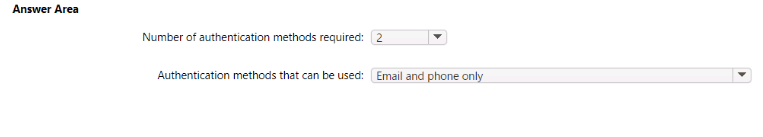
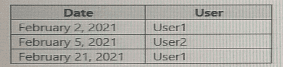
You create the Azure Active Directory (Azure AD) users shown in the following table.
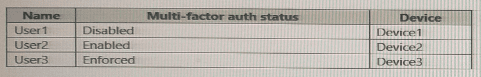
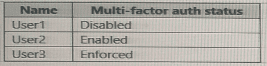
On February 1, 2021, you configure the multi-factor authentication (MFA) settings as shown in the following exhibit.
The users authentication to Azure AD on their devices as shown in the following table.
On February 26, 2021, what will the multi-factor auth status be for each user?
A)
B)
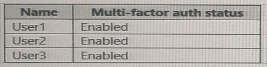
C)

D)

Answer : B
You have a Microsoft 365 E5 subscription.
You deploy a third-party web gateway named Gateway1.
You need to integrate Gateway1 with Microsoft Defender for Cloud Apps. The solution must meet the following requirements:
Ensure that data flows automatically to Defender for Cloud Apps.
Minimize administrative effort.
What should you do first?
Answer : D
Comprehensive and Detailed In-Depth
Let's break this down step by step based on Microsoft Defender for Cloud Apps (MDCA) integration with third-party web gateways, as outlined in Microsoft Identity and Access Administrator documentation.
Understanding the Scenario and Requirements:
Microsoft 365 E5 subscription:This subscription includes Microsoft Defender for Cloud Apps, which provides the necessary licensing for integrating with third-party web gateways.
Third-party web gateway named Gateway1:A web gateway (e.g., a Secure Web Gateway like Zscaler, Netskope, or Symantec) is deployed to manage and secure internet traffic. The question does not specify the vendor, but the process for integration with MDCA is generally the same for supported gateways.
Requirement:Integrate Gateway1 with Microsoft Defender for Cloud Apps to ensure that data (e.g., traffic logs, events) flows automatically to MDCA for analysis, visibility, and policy enforcement. The solution must also minimize administrative effort.
Microsoft Defender for Cloud Apps supports integration with third-party web gateways to provide visibility into cloud app usage, detect shadow IT, and enforce security policies. This integration typically involves collecting logs from the gateway for analysis in MDCA.
How Microsoft Defender for Cloud Apps Integrates with Third-Party Web Gateways:
MDCA can integrate with third-party web gateways by collecting logs that contain traffic data (e.g., user activity, app usage, IP addresses). This allows MDCA to analyze the data and provide insights into cloud app usage, detect threats, and enforce policies.
The primary method for integrating a third-party web gateway with MDCA is toadd a log collector. This involves:
Configuring the web gateway to send logs to a log collector (e.g., via Syslog or FTP).
Setting up a log collector in MDCA to receive and process these logs.
Once configured, the log collector automatically pulls logs from the web gateway, ensuring that data flows to MDCA for analysis.
This method supports automatic data flow and minimizes administrative effort because, after the initial setup, the log collection process runs continuously without manual intervention.
Analyzing the Options:
A . Add a data source:
In Microsoft Defender for Cloud Apps, 'data sources' typically refer to sources of user activity data, such as Microsoft Entra ID audit logs, Microsoft 365 audit logs, or other Microsoft services. Adding a data source in MDCA is used to import user activity data for correlation with cloud app usage, but it is not the mechanism for integrating a third-party web gateway.
Third-party web gateways are not considered 'data sources' in MDCA; instead, they are integrated via log collectors.
Conclusion:This option is incorrect because adding a data source does not facilitate integration with a third-party web gateway like Gateway1.
B . Create an app registration:
Creating an app registration in Microsoft Entra ID is typically used to integrate cloud apps with MDCA for session control (e.g., via Conditional Access App Control) or to enable API-based log collection for supported apps (e.g., Salesforce, Box).
However, a third-party web gateway like Gateway1 is not a cloud app that requires an app registration. Web gateways are network appliances or services that manage traffic, and their integration with MDCA involves log collection, not app registration.
Conclusion:This option is incorrect because creating an app registration is not relevant to integrating a web gateway with MDCA.
C . Create a snapshot report:
A snapshot report in MDCA is a manual process where an administrator uploads a log file (e.g., a CSV or JSON file) from a third-party service to analyze cloud app usage. This is a one-time, manual process used for discovery (e.g., to identify shadow IT).
The requirement specifies that data must flow 'automatically' to Defender for Cloud Apps, and a snapshot report does not meet this requirement because it requires manual uploads each time. It also does not minimize administrative effort due to the ongoing manual intervention.
Conclusion:This option is incorrect because creating a snapshot report does not enable automatic data flow and increases administrative effort.
D . Add a log collector:
Adding a log collector in Microsoft Defender for Cloud Apps is the standard method for integrating third-party web gateways. MDCA supports log collection from many web gateways (e.g., Zscaler, Netskope, Symantec) via Syslog or FTP.
Process:
In the Microsoft Defender for Cloud Apps portal, navigate toSettings > Log collectors.
Add a new log collector, specifying the protocol (e.g., Syslog over TCP/UDP or FTP) and the details of the web gateway (e.g., IP address, port).
Configure Gateway1 to send logs to the log collector (this step is done on the Gateway1 side, typically by the network team).
Once set up, the log collector automatically collects logs from Gateway1 and processes them in MDCA for analysis.
Automatic Data Flow:The log collector ensures that data flows automatically to MDCA, meeting the first requirement.
Minimize Administrative Effort:After the initial setup, the log collector runs continuously without manual intervention, minimizing administrative effort.
Conclusion:This option is correct because adding a log collector is the first step to integrate Gateway1 with MDCA, ensuring automatic data flow and minimizing administrative effort.
Why 'Add a log collector' is the First Step:
The question asks for the first step to integrate Gateway1 with Microsoft Defender for Cloud Apps. Adding a log collector is the initial action in MDCA to enable log collection from a third-party web gateway.
Subsequent steps (not asked in the question) would include configuring Gateway1 to send logs to the log collector, but this is done outside MDCA (e.g., in Gateway1's management console). The question focuses on the action in MDCA, making 'Add a log collector' the correct first step.
Additional Considerations:
The question does not specify the vendor of Gateway1, but Microsoft Defender for Cloud Apps supports log collection from many third-party web gateways (e.g., Zscaler, Netskope, Symantec, Cisco Umbrella). The process is the same regardless of the vendor, as long as the gateway supports Syslog or FTP log export.
If Gateway1 were not a supported web gateway, additional steps (e.g., custom log parsing) might be required, but the question implies Gateway1 can be integrated using standard methods.
The Microsoft 365 E5 subscription includes Microsoft Defender for Cloud Apps, so no additional licensing is required.
Conclusion:To integrate Gateway1 with Microsoft Defender for Cloud Apps, ensuring that data flows automatically and minimizing administrative effort, the first step is toadd a log collectorin MDCA. This sets up the infrastructure to receive logs from Gateway1, enabling automatic data flow for analysis. Therefore, the correct answer isD.
Microsoft Defender for Cloud Apps documentation: 'Integrate with a third-party web gateway' (Microsoft Learn:https://learn.microsoft.com/en-us/defender-cloud-apps/connect-third-party-gateway)
Microsoft Defender for Cloud Apps documentation: 'Set up a log collector' (Microsoft Learn:https://learn.microsoft.com/en-us/defender-cloud-apps/log-collector)
You have a Microsoft Entra tenant.
You need to implement smart lockout with a lockout threshold of 10 failed sign-ins. What should you configure in the Microsoft Entra admin center?
Answer : B
You have a Microsoft 36S subscription. The subscription contains users that use Microsoft Outlook 2016 and Outlook 2013 clients. You need to implement tenant restrictions. The solution must minimize administrative effort. What should you do first?
Answer : A
Your company purchases 2 new Microsoft 365 ES subscription and an app named App.
You need to create a Microsoft Defender for Cloud Apps access policy for App1.
What should you do you first? (Choose Correct Answer based on Microsoft Identity and Access Administrator at microsoft.com)
Answer : D
https://learn.microsoft.com/en-us/defender-cloud-apps/access-policy-aad
To create a Microsoft Defender for Cloud Apps access policy for App1, you should configure aConditional Access policy to use app-enforced restrictions. This will allow you to control access to your cloud apps based on conditions such as user, device, location, and app state. You can also use app-enforced restrictions to control access to your cloud apps based on the state of the app, such as whether it's running on a managed or unmanaged device.
SIMULATION
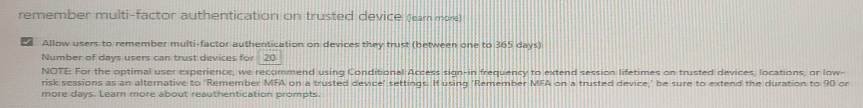
You implement the planned changes for SSPR.
What occurs when User3 attempts to use SSPR? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
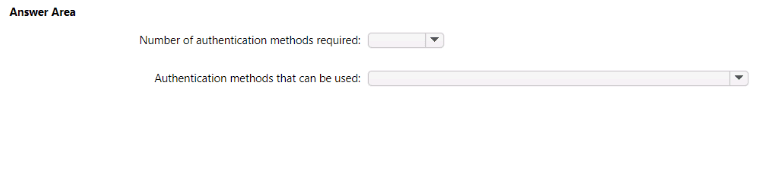
Answer : A
Answer is