NetApp Certified Implementation Engineer - SAN Specialist, E-Series NS0-516 Exam Questions
What is the minimum number of drives needed to create a Dynamic Disk Pool?
Answer : A
To create a Dynamic Disk Pool (DDP), the minimum number of drives required is 12. This minimum requirement ensures that there is enough capacity and redundancy to maintain the performance and data protection characteristics that DDPs provide.
Dynamic Disk Pools are designed to optimize data distribution and rebuild times. By using 12 drives as a baseline, the system can efficiently distribute data and parity information across the drives, improving fault tolerance and rebuild performance compared to traditional RAID configurations.
NetApp E-Series Storage System Documentation
SANtricity System Manager User Guide
You are adding drives to an existing Dynamic Disk Pool (DDP).
In this scenario, which two drive characteristics should you consider when selecting the drives? (Choose two.)
Answer : A, B
Check Drive Capacity:
Step: Ensure that the new drives are of the same capacity or larger than the existing drives in the DDP.
Reason: Consistent drive capacity ensures optimal performance and utilization.
Verify Security Type:
Step: Confirm that the new drives have a compatible security type (e.g., FDE, FIPS) with the existing drives.
Reason: Incompatible security types can lead to configuration issues or reduced security.
NetApp E-Series Hardware and Software Compatibility Guide
NetApp SANtricity System Manager User Guide
Click the Exhibit button.
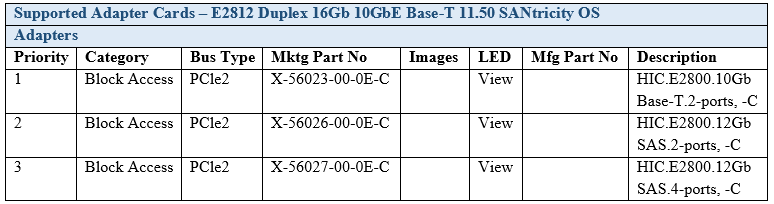
You ordered a NetApp E2812 Duplex 16GB 10 GbE Base-T system.
Referring to the exhibit, what is the maximum number of 10GbE Base-T ports available to be used?
Answer : B
The exhibit shows the supported adapter cards for the E2812 system with specific marketing part numbers.
The E2812 system ordered is a Duplex 16Gb 10GbE Base-T system with the adapter card part number X-56023-00-0E-C, which is described as 'HIC.E2800.10Gb Base-T.2-ports, -C'.
Each card provides 2 ports.
Given that the system is duplex, it means it has two controllers, each capable of supporting one card.
Therefore, each controller can have one 10GbE Base-T card with 2 ports, resulting in a maximum of 4 ports available in total for the system.
NetApp E-Series SANtricity System Manager and E2800 Series Hardware Installation Guide.
A company is using the Federal Information Processing Standard (FIPS) on all volume groups. However, one volume group failed a security audit.
In this scenario what would cause a volume group to fail the security audit?
Answer : A
FIPS Compliance: The Federal Information Processing Standard (FIPS) requires all components within a system to adhere to specific security standards.
FDE Drives: Full Disk Encryption (FDE) drives are used to ensure data security.
Audit Failure: Adding an FDE drive as a spare to a volume group without proper encryption settings could cause a security audit to fail.
Solution: Ensure all spare drives in a volume group meet the FIPS encryption requirements.
You are cabling drive expansion shelves for an E2800 storage system.
In this scenario, which cabling method should you use?
Answer : B
Cabling method: It is important to distribute the connections for redundancy and balanced performance.
EXP1 and EXP2 ports: By dividing these ports between the A-side and B-side IOM-12 modules, the system ensures balanced load and failover capabilities.
Reference: NetApp E-Series hardware setup and configuration guide.
Click the Exhibit button.
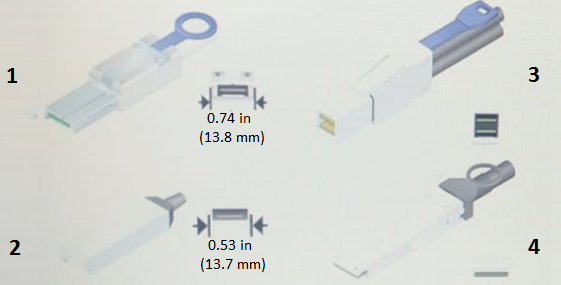
Referring to the exhibit, which SAS connector is supported on the NetApp E2800 E-Series family?
Answer : A
Identify SAS Connector Types: The exhibit shows different types of SAS connectors labeled 1 through 4.
Review E2800 Documentation: According to NetApp E2800 E-Series documentation, the supported SAS connector for expansion and host connectivity is type 1, which is the mini-SAS HD (High Density) connector.
Match the Connector: Verify the appearance and dimensions of the connector in the exhibit. Type 1 matches the mini-SAS HD connector used in the E2800 series.
Confirm Selection: Type 1 (0.74 in / 13.8 mm) is the correct choice for the E2800 family based on the physical characteristics and NetApp specifications.
A customer wants to manage an E-Series system over a secure connection between the system and a server. During implementation, you are asked to fulfill this installation requirement.
In this scenario, which three actions are required to complete this task? (Choose three.)
Answer : A, C, E
Secure Connection Requirement: To manage the E-Series system over a secure connection, certain steps need to be taken to ensure encrypted communications.
Disabling Legacy Management Interface: This step ensures that only secure management interfaces are used, preventing the use of less secure legacy protocols.
Certificate Signing Request (CSR): Completing the CSR on the system is necessary to generate a public/private key pair. This CSR can then be submitted to a certificate authority (CA) to obtain a signed certificate.
Importing CA Signed Certificates: Once the CA has signed the certificate, it must be imported into the E-Series system. This signed certificate ensures that the communication between the server and the system is encrypted and trusted.
NetApp E-Series SANtricity System Manager documentation on secure management
NetApp Implementation Engineer - SAN Specialist - E-Series manuals