Nutanix Certified Professional - Data Services NCP-DS Exam Questions
A company uses a Nutanix 3-node cluster environment. In Prism Pro, the Capacity Runway
shows these capacity values:Max Capacity 6 TiB Effective Capacity 4 TiB
The company wants to upgrade the environment to use an RF3 container and also requires all
cluster nodes to be the same model.
What must the effective capacity of the Nutanix cluster be to support the new RF3 container?
Answer : A
An administrator needs to upgrade Files in a dark site environment without LCM, Which set of actions should the administrator perform?
Answer : C
Refer to the exhibit.
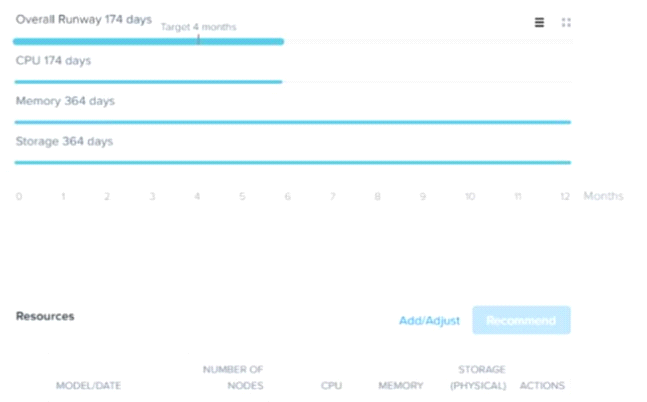
An administrator has been informed that a new workload will be deployed in six months with these characteristics.
* CPU: 210 GHz
* Memory: 600 GiB
* Storage:11.72 TiB
Upon receiving the new project notification, the administrator creates a scenario to determine whether or not the Nutanix cluster has enough space capacity to properly handle the new workload.
Why is the Overall Cluster runway showing that cluster resources are not exhausted (red color)?
Answer : D
https://support-portal.nutanix.com/page/documents/details?targetId=Prism-CentralGuide-Prismv5_19:mul-resource-planning-runway-view-pc-r.html
A company is implementing Files and has these requirements
* Six departments
* Each department needs to access its own shared namespace
* 18,000 users
Given the nature of the workload the administrator has decided to scale up by adding the
maximum amount of CPU and RAM
What should the administrator implement to satisfy the stated requirements?
Answer : D
A storage administrator has been given the task of migrating data from an old storage system
to a Files scale-out system. While assessing the assigned task the administrator notes that 2000
home directories with VSS enabled need to be migrated
How should the administrator satisfy this need?
Answer : B
An administrator needs to configure Windows Server Failover Clustering (WSFC) in a Nutanix
environment using storage provided by the Nutanix cluster.
Which two prerequisites are required to accomplish this task? (Choose two.)
Answer : A, D
An administrator is implementing a storage solution with these requirements:
* Is easily searchable
* Natively supports disaster recovery * Access to each item needs to be fast
* Can scale to petabytes of data
* Users are granted access after authentication * User data is isolated, but could be shared
How should the administrator satisfy these requirements?
Answer : C