Palo Alto Networks SD-WAN Engineer SD-WAN-Engineer Exam Questions
When planning a software upgrade for a large fleet of ION devices, what is the recommended best practice regarding the "Software Version" assigned in the Site Summary?
Answer : C
Comprehensive and Detailed Explanation
The best practice for managing upgrades in a large-scale Prisma SD-WAN environment is the Canary or Phased Rollout approach, utilizing Site Tags.
Risk Mitigation: Upgrading all sites simultaneously (Option B) is highly risky. If the new software version has an unforeseen bug or compatibility issue with a specific circuit type, the entire network could face an outage.
Tag-Based Management: Administrators should create tags such as 'Upgrade-Phase-1' (Pilot sites) or 'Region-North'. By assigning the specific Software Version to the Tag (rather than the individual site or the global default), the controller pushes the update only to that subset of devices.
Procedure:
Apply update to 'Pilot' tag (5 sites). Monitor for 24-48 hours.
Apply update to 'Region-1' tag (50 sites). Monitor.
Eventually, update the Global default once confidence is high.
Option A is unscalable, and Option D is incorrect as the administrator retains full control over when upgrades occur; they are not forced automatically without policy configuration.
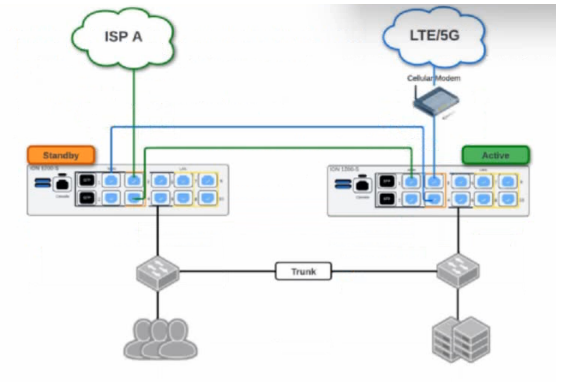
Based on the HA topology image below, which two statements describe the end-state when power is removed from the ION 1200-S labeled ''Active'', assuming that the ION labeled ''Standby'' becomes the active ION? (Choose two.)
Answer : A, C
Prisma SD-WAN High Availability (HA) for branch ION devices, particularly the Gen-2 ION 1200-S, is designed to provide '100% WAN Capacity' preservation during a hardware or power failure. This is achieved through the use of Bypass Pairs (Fail-to-Wire). In the provided topology, the ISP A and LTE/5G circuits are cross-connected using the bypass ports (typically ports 3 and 4 on the ION 1200-S).
When the 'Active' ION device loses power, the internal physical relays in its bypass ports transition to a closed state, effectively creating a physical bridge between the ports. In this scenario, the LTE/5G signal---which enters the Active ION's port 4---is mechanically bridged to port 3, allowing it to pass through to port 4 of the Standby ION. Simultaneously, ISP A is already connected to the Standby ION. Consequently, once the Standby device completes its transition to the 'Active' state, it has physical access to both WAN circuits, validating Statement A.
Regarding the LAN transition, Prisma SD-WAN does not use standard VRRP for ION-to-ION HA; instead, it uses a proprietary Control Plane HA mechanism. When the failover occurs, the newly active ION takes over the IP addresses of all configured Switch Virtual Interfaces (SVIs) and LAN interfaces. To ensure the downstream Layer 2 infrastructure (like the LAN switches shown in the diagram) updates its MAC address tables to point to the new physical hardware for those IPs, the newly active ION immediately broadcasts a Gratuitous ARP (GARP). This ensures that LAN traffic is correctly steered to the new device without a significant timeout, validating Statement C.
Which action meets the needs of an organization that requires elevated incident notifications for its headquarters location?
Answer : C
In the Prisma SD-WAN (Instant-On Network) management framework, administrators can customize how events are handled and prioritized across different sites through Event Policies. An organization that requires 'elevated incident notifications' for a critical site like its headquarters needs a way to differentiate those alerts from standard branch notifications in the management portal and integrated third-party tools.
The most direct and effective method to achieve this is by configuring an Event Policy Rule specifically for the headquarters site. Within the incident policy framework, administrators can create rules that match specific resources---in this case, the headquarters site---and apply an action to set the priority. Priority levels typically range from P1 (highest) to P5 (lowest).1 By setting these to the highest level (P1), any generated incident for that site will immediately stand out on the dashboard as a high-priority event.
This approach is superior to other options because it changes the inherent importance of the alert within the Prisma SD-WAN logic itself. For example, a 'WAN Link Down' event at a small retail branch might be a P3, but the same event at the HQ could be elevated to a P1 via a custom policy rule. This elevation ensures that the Network Operations Center (NOC) is alerted more urgently and that external integrations, such as ServiceNow or PagerDuty, receive the correct priority mapping for immediate escalation. Options such as aggressive SLA thresholds (Option B) only increase the frequency of alerts, not necessarily their notification priority, while global syslog or SNMP settings (Options A and D) lack the site-specific granularity required for this use case.
What are two requirements for implementing user/group-based path policies? (Choose two.)
Answer : A, D
Comprehensive and Detailed Explanation
To implement User/Group-based policies (Path, QoS, or Security) in Prisma SD-WAN, the system requires two specific components to resolve user identities and map them to IP addresses within the fabric.
Cloud Identity Engine (CIE): This is the primary requirement for identity management. The Cloud Identity Engine connects the Prisma SD-WAN controller to your directory service (e.g., Active Directory, Azure AD/Entra ID). It allows the system to retrieve and resolve User and Group attributes (e.g., 'Marketing Group,' 'User: john.doe') so they can be selected in policy rules. Without CIE, the controller cannot interpret the group names or user identities defined in the policies.
Data Center ION: In the standard deployment model for User-ID, a Data Center (DC) ION is required to act as the bridge or collector for IP-to-User mappings. The DC ION connects to the User-ID Agent (running on a PAN-OS firewall or Windows Server) to learn the mapping of IP addresses to usernames. It then redistributes this information to the controller or other branch IONs so they can identify which user is associated with the traffic flows originating from a specific private IP address.
Which condition, when configured within a performance policy, is a trigger for generating an incident related to application performance or path degradation?
Answer : A
In Prisma SD-WAN, Performance Policies are the primary mechanism used to define the expected quality of experience for specific applications. Unlike traditional monitoring that relies solely on 'up/down' interface states, Prisma SD-WAN focuses on the actual health of the application path. An incident is triggered when the system detects a violation of defined service-level agreement (SLA) thresholds, such as excessive latency, jitter, or packet loss, even if the physical link remains active.
When an administrator configures a performance policy, they set specific bounds for these metrics. For example, a VoIP application might have an SLA requiring latency below 150ms and packet loss below 1%. If the ION device detects that the current path (e.g., a broadband circuit) exceeds these limits, it generates a performance incident. This incident serves two purposes: first, it alerts the administrator to the degradation; second, it triggers the Path Selection engine to proactively steer the application traffic to a more suitable 'Backup' or 'Available' path that currently meets the SLA requirements.
Options B, C, and D represent system-level or network-level events that generate different types of alerts or incidents (System or Network incidents), but they are not the triggers defined within a Performance Policy. Performance policies are specifically concerned with the application's perceived performance across the fabric. By focusing on SLA violations rather than just physical link status, Prisma SD-WAN ensures that business-critical applications remain functional even during 'brownout' conditions where a circuit is technically 'up' but performing poorly.
Where is route leaking configured between VRFs?
Answer : D
In the Prisma SD-WAN solution, multi-tenancy and network isolation are achieved through the use of Virtual Routing and Forwarding (VRF) instances. However, there are many operational scenarios---such as providing shared access to a common service (e.g., DNS, NTP) or a central Internet gateway---where traffic must transition between these isolated routing domains. This process is known as route leaking.
In the Prisma SD-WAN management interface, route leaking is specifically configured within the VRF Profile. Unlike traditional CLI-based routers where route leaking might be configured under a global routing table or individual VRF definitions via import/export targets, Prisma SD-WAN utilizes a profile-based approach to ensure scalability and consistency across multiple sites. A VRF Profile acts as a template that defines the routing behavior for specific VRFs across the fabric.
When an administrator navigates to the VRF Profile settings, they can define 'Leaking Rules.' These rules specify the 'From VRF' (source) and 'To VRF' (destination) parameters, along with the specific prefixes or default routes that should be shared. By placing this configuration within the VRF Profile rather than a site-specific configuration, Palo Alto Networks allows for a 'configure once, apply many' workflow. Once the VRF Profile is updated with the leaking rules, any ION device associated with that profile will automatically update its local routing table to allow the specified inter-VRF communication. This centralized orchestration simplifies the management of complex segmentation requirements in large-scale SD-WAN deployments.
When integrating Prisma SD-WAN with Prisma Access, what is the specific role of the Service Connection (SC)?
Answer : A
Comprehensive and Detailed Explanation
In the Prisma Access architecture (integrated with SD-WAN), distinct connection types serve different purposes.
Remote Networks: These are the connections from your Branch sites (using ION devices) into the cloud. They allow branches to get to the internet or other branches.
Service Connections (SC): This is a specialized high-bandwidth connection used to bridge the Prisma Access Cloud to your Private Data Center or Headquarters.
The primary use case for a Service Connection (Option A) is to allow mobile users and branch users (who are connected to the Prisma cloud) to reach private, centralized resources that still reside on-premise, such as Active Directory controllers, legacy databases, or mainframes. Without a Service Connection, users in the cloud would be able to reach the internet and each other, but not the servers physically located in your HQ data center. The CloudBlade automates the creation of these tunnels, but architecturally, the 'Service Connection' is the 'cloud-to-HQ' bridge.