Palo Alto Networks XSIAM Engineer XSIAM-Engineer Exam Questions
A Cortex XSIAM engineer adds a disable injection and prevention rule for a specific running process. After an hour, the engineer disables the rule to reinstate the security capabilities, but the capabilities are not applied.
What is the explanation for this behavior?
Answer : A
When a disable injection and prevention rule is applied to a running process, the security capabilities are detached for the lifetime of that process. Even after disabling the rule, the capabilities are not reapplied automatically; the process must be restarted to restore security enforcement.
A Cortex XSIAM engineer plans to add Kafka and Syslog Collectors to a Broker VM cluster.
What are two expected behaviors of the applets when they are added to the cluster? (Choose two.)
Answer : A, D
In a Broker VM cluster, the Syslog Collector applet runs in active/standby mode (active on the primary node, standby on others), while the Kafka Collector applet runs in active/active mode (active on all nodes). This design ensures both high availability and scalability for ingestion.
What is the role of "in" in the query line below?
action_local_port in (1122, 2234)
Answer : B
In the query action_local_port in (1122, 2234), the word 'in' functions as an operator. It checks whether the field action_local_port matches any value in the specified list (1122, 2234).
In which two locations can correlation rules be monitored for errors? (Choose two.)
Answer : A, B
Correlation rule errors can be tracked in XDR Collector audit logs (type = Rules, subtype = Error) and by querying the correlations_auditing dataset through XQL. These provide visibility into execution issues and failures for correlation rules.
An application which ingests custom application logs is hosted in an on-premises virtual environment on an Ubuntu server, and it logs locally to a .csv file.
Which set of actions will allow the ingestion of the .csv logs into Cortex XSIAM directly from the server?
An application which ingests custom application logs is hosted in an on-premises virtual environment on an Ubuntu server, and it logs locally to a .csv file.
Which set of actions will allow the ingestion of the .csv logs into Cortex XSIAM directly from the server?
Answer : A
The correct approach is to install a Broker VM in the environment and configure its CSV Collector applet to ingest the .csv log files directly from the Ubuntu server. This enables secure ingestion of custom application logs into Cortex XSIAM without modifying the application or requiring an XDR agent on the server.
What is the function of the "MODEL" section when creating a data model rule?
Answer : D
The MODEL section in a data model rule is used to map log fields to the corresponding Cortex XSIAM Data Model (XDM) fields. This ensures that ingested data aligns with XDM, enabling consistent analytics, detections, and queries across different data sources.
Based on the _raw_log and XQL query information below, what will be the result(s) of the temp_value?
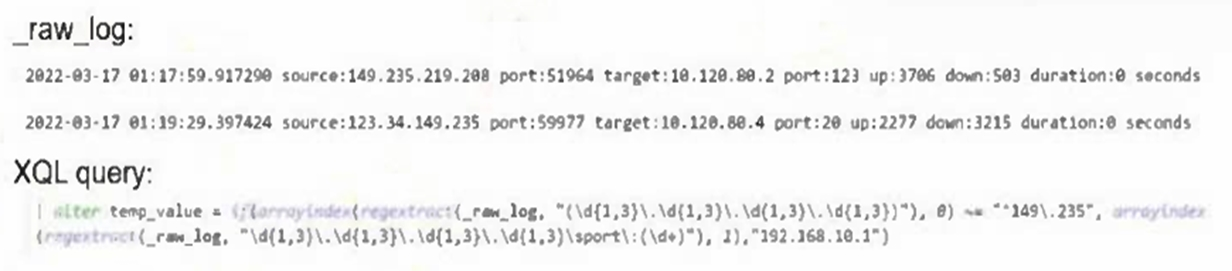
Answer : A
The XQL query uses regextract with conditions to check if the source IP begins with 149.235. When true, it assigns the replacement value 192.168.10.1, otherwise it extracts the source port. From the given logs, this produces 123 (from the port extraction in the second log) and 192.168.10.1 (replacement for the first log's matching source IP).