Proofpoint Certified Threat Protection Analyst PPAN01 Exam Questions
Why do some domains generate a warning when they are added to the custom blocklist in TAP?
Answer : D
TAP URL Defense custom blocklists can accept domain-based entries, but Proofpoint warns when you attempt to block domains that are widely used by legitimate services (D). Blocking an entire ''popular/prominent'' domain (or a broad wildcard that matches it) can cause major business disruption: break SaaS access, block legitimate customer/vendor communications, and generate a flood of user tickets---ultimately harming containment efforts by forcing emergency rollback. In Proofpoint-focused IR, the safest containment approach is precision: block the specific malicious domain, subdomain, or path pattern when supported, and avoid blanket blocks that collide with common web platforms (cloud storage, URL shorteners, collaboration tools). The warning is a guardrail to prevent overly broad mitigations that create operational outages while providing limited security benefit (attackers can shift infrastructure quickly). When a threat leverages a legitimate platform, IR teams typically prefer tighter controls: block the exact malicious host, apply time-of-click blocking, use isolation/safe browsing controls, and hunt/pull the related emails rather than blocking the entire service domain.
A college student receives the email shown in the exhibit.
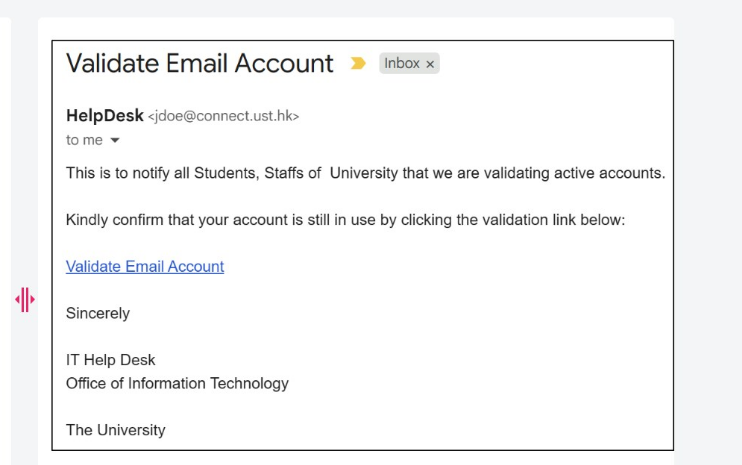
What type of attack is being performed?
Answer : B
This is a classic phishing lure (''Validate Email Account'') where the attacker aims to create trust by presenting a familiar-looking sender identity to the recipient. In many real phishing waves, attackers manipulate what the user visually trusts first: the friendly name (display name) shown by mail clients. ''Display Name Spoofing'' is specifically when the attacker sets the From display name to something authoritative (e.g., ''HelpDesk'', ''IT Support'', ''University Admin'') while the underlying sender address may not be an approved helpdesk identity, or may be a compromised mailbox that is not actually the IT department. Proofpoint IR review commonly verifies this by comparing: (1) the displayed name, (2) the RFC5322.From address, and (3) authentication results (SPF/DKIM/DMARC) plus ''Header From vs Envelope From'' alignment. Lookalike domain focuses on deceptive domains (e.g., great-c0mpany.com) rather than the visible name; Reply-To spoofing requires a mismatched Reply-To field, which is not the primary indicator shown in the exhibit. For response, analysts prioritize user notification, link detonation/URL Defense verdicts, and retroactive search-and-pull (TRAP/CTR) if delivered.
What is the purpose of Smart Search?
Answer : B
Smart Search is a message-tracing and investigation feature used to query and analyze email messages processed by Proofpoint's email security pipeline (B). In Proofpoint-focused IR, it functions as a primary evidence source for determining whether a message was accepted, rejected, quarantined, rewritten (URL Defense), modified (banners), or delivered, and which policy/rule triggered the decision. Analysts use Smart Search to pivot on sender/recipient, subject, message IDs, attachment names/hashes, URLs, sending IPs, and disposition outcomes---supporting rapid scoping (who got it, how many, what happened) and timeline creation. This is essential for detection and analysis because it links threat intelligence (from TAP verdicts) to operational mail flow facts (gateway decisions). It is not a host forensics tool (files downloaded), a web click-tracing platform (though TAP provides click telemetry), or a network firewall analysis console. In practice, Smart Search accelerates false positive validation, identifies false negatives (delivered when it should have been blocked), and provides the authoritative audit trail needed for containment actions and post-incident reporting.
Exhibit:
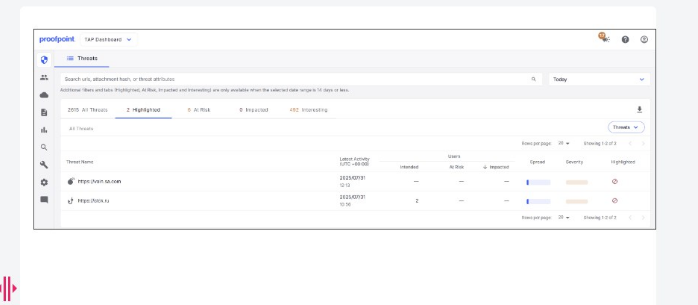
What is indicated by the icon shown in the ''Highlighted'' column?
Answer : C
In the TAP Dashboard, the ''Highlighted'' column is used to surface items that require analyst attention beyond basic volume metrics, including items that have been explicitly flagged for investigation outcomes. The icon shown corresponds to a false positive report (C), meaning the message or threat classification is being contested as benign but incorrectly condemned or prioritized as malicious. In Proofpoint workflows, this matters because false positives can disrupt business operations (legitimate suppliers, customer mail, internal systems) and can also hide real threats if analysts become desensitized to noisy alerting. Handling a highlighted false positive typically involves validating message authentication (SPF/DKIM/DMARC), reviewing TAP verdict drivers (URL/attachment detonation, reputation, MLX scoring where applicable), and confirming business legitimacy (known sender relationship, expected content, and user confirmation). When confirmed, analysts submit false positive feedback through the correct channel to improve future detection fidelity and reduce repeat quarantines. Operationally, false positive handling is part of detection hygiene: it improves signal quality, reduces alert fatigue, and ensures that high-confidence threats rise to the top of the triage queue.
When filtering for threats on the TAP People page, which two filters have the highest chance of finding compromises? (Select two.)
Answer : A, C
Compromise likelihood increases sharply when users both (1) received a threat that remained accessible and (2) successfully interacted with it. ''Exposure > Permitted Clicks'' (A) directly indicates that a user clicked a rewritten/protected URL and the click was permitted (not blocked), which is one of the strongest leading indicators for credential theft or malware execution pathways. ''Exposure > Delivered with Accessible Threat'' (C) indicates delivery of a message that still contained an accessible malicious component at the time of access (e.g., URL remained reachable/uncleared), raising the chance of interaction leading to compromise. In Proofpoint IR, these two filters are used to rapidly build a ''likely compromised'' watchlist for immediate follow-up: validate click details, check for credential submission, correlate with suspicious logins, review mailbox rules/forwarding, and trigger post-delivery remediation (quarantine/pull) if copies remain. ''Users > VIP'' is important for business impact, but VIP status alone doesn't indicate compromise. ''False Positives Only'' reduces compromise likelihood by definition, and location filtering is contextual---not a direct compromise signal.
What is the primary function of the People Page in the Threat Protection Workbench and TAP Dashboard?
Answer : D
The People Page is a user-centric investigation view designed to help analysts quickly identify who is being targeted and who is most at risk/impacted by threats (D). Instead of starting from a single message, responders can pivot from user risk signals---Attack Index, exposure metrics, click behavior, VIP status, and repeated campaign targeting---to build a prioritized queue for investigation. In Proofpoint IR operations, this supports rapid triage during active phishing/BEC waves: analysts identify the highest-risk users first (those with permitted clicks or delivered accessible threats), then perform immediate follow-up actions such as credential resets, session/token revocation, mailbox rule review, and targeted comms. The People Page is not an access control manager and it is not the place to configure granular filtering rules per user (that's policy/admin territory). It's also distinct from security awareness simulation dashboards, though it can inform who should receive training based on risky behavior. As part of detection and analysis, the People Page helps convert large-scale threat telemetry into actionable, person-focused response steps, minimizing dwell time and reducing the chance that the most exposed users are missed.
Where can a user access ''Smart Search''? (Select two.)
Answer : A
Smart Search is a message-tracing and investigation capability used to locate and analyze email messages processed by Proofpoint email security components. Practically, responders use it to pivot on sender, recipient, subject, message ID, IPs, URLs, and dispositions to rapidly scope incidents (who received what, what action was taken, whether it was quarantined/rejected/delivered) and to support response actions (block, release, or escalate). In Proofpoint deployments, Smart Search is accessible in the Protection Server administrative interface (on-prem PPS) and in the Email Protection cloud administrative experience (Proofpoint Email Protection / PoD admin), aligning to where message processing and policy decisions are recorded. TAP Dashboard is primarily threat-focused telemetry (URLs, attachments, campaigns, user exposure), while TRAP/Threat Response consoles are centered on post-delivery remediation and orchestration. For IR, knowing the correct consoles matters because message trace data is authoritative for chain-of-events reconstruction: it provides time stamps, policy hits, verdicts, and routing outcomes needed for incident timelines and validation of false positives/negatives. Correct access points ensure analysts can quickly confirm whether the gateway acted as expected and whether any delivered mail requires retroactive remediation.