SailPoint Certified IdentityNow Engineer IdentityNow-Engineer Exam Questions
Exhibit.
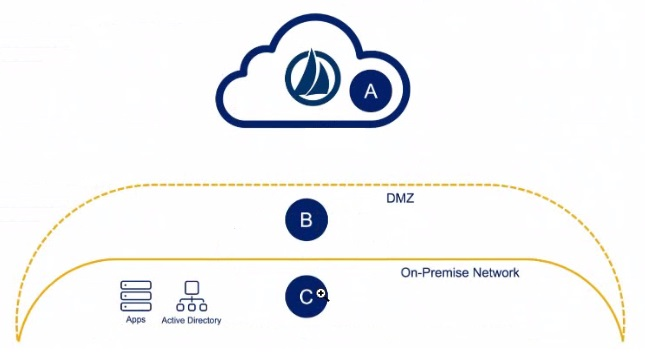
Solution: An engineer has one small production data center with an Active Directory, a database server, and two cloud applications to which they need to connect Where would the virtual appliances (VAs) reside In this scenario?
Solution: A
Answer : B
No, the Virtual Appliances (VAs) should not reside in A, which represents the SailPoint cloud environment. VAs are typically deployed in the on-premises network to interface directly with internal resources like Active Directory, databases, and applications. The cloud environment is where IdentityNow services are hosted, but the VAs need to be positioned closer to on-premise resources to manage identity synchronization and provisioning tasks.
Key Reference from SailPoint Documentation:
VA Placement Recommendations: Virtual Appliances are deployed in the on-premise network rather than the cloud, to ensure they have direct and secure access to internal resources.
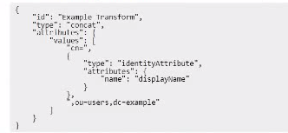
Review the following transform:
Can the following output of this transform be expected, based on the input provided in the option?
Solution:
Answer : A
The provided transform is of type 'Concat', which means it concatenates values from multiple sources. In this case, it appears to be concatenating the 'cn' value with the 'displayName' attribute of an identity. The 'type': 'IdentityAttribute' section specifies that the transform is pulling the 'displayName' attribute from the identity object.
Given the input where the displayName is 'Thomas Miller', the expected output is in the format cn=Thomas Miller,ou=users,dc=example, which aligns with the displayed output in the example. The transformation concatenates the displayName value with the rest of the distinguished name (DN), which is a common use case for generating a DN from user attributes.
Key Reference from SailPoint Documentation:
Concat Transform in IdentityNow: The concat transform is used to join multiple attribute values, and in this example, it successfully creates the expected DN string using the provided displayName input.
An IdentityNow engineer has set up an access profile for an application. The access profile allows for users to request access, and for a user's manager to approve or deny access.
After a recent staff meeting, management has expressed that they want to remove any approval requirements for this application.
Is management's request possible in IdentityNow. and. if so. are these the recommended steps the engineer should take to meet their new requirement?
Solution: It is possible. Delete the access profile.
Answer : B
No, deleting the access profile is not the correct way to meet the requirement of removing approval for access requests. The access profile defines the entitlements and permissions that users can request for an application. Deleting it would remove the entire ability to request access, rather than just removing the approval workflow. The correct step would be to modify the approval settings in the access profile (as explained in Question 44), not to delete it.
Key Reference from SailPoint Documentation:
Access Profile Management: Modifying approval settings in the access profile is the appropriate step to meet management's new requirement, not deleting the profile itself.
Does this run on the VA?
Solution: IQService
Answer : B
IQService does not run on the Virtual Appliance (VA). It is a separate service that must be installed on a Windows Server within the environment that has access to the target system, particularly for Active Directory and other Windows-based systems. IQService acts as a proxy between the IdentityNow tenant and these target systems, allowing operations such as password management and account provisioning to be executed on systems that do not support native connectors on the VA. It communicates with the VA but is not hosted on it.
SailPoint IdentityNow IQService Installation Guide.
SailPoint IdentityNow Target Connector Architecture.
Is this statement correct about security and/or encryption of data?
Solution: When setting up a virtual appliance cluster. SailPoint creates an asymmetnc key pair based on a user-provided passphrase. and then uses this key pair to communication with the IdentityNow tenant.
Answer : A
Yes, this statement is correct. When setting up a Virtual Appliance (VA) cluster, SailPoint does indeed create an asymmetric key pair based on a user-provided passphrase. This key pair is used for secure communication between the Virtual Appliance and the IdentityNow tenant. The asymmetric encryption model uses a public-private key pair where the private key is stored securely within the VA, and the public key is shared with the IdentityNow tenant to establish a secure, encrypted communication channel. This setup ensures that data exchanged between the VA and the IdentityNow tenant remains protected.
SailPoint IdentityNow Virtual Appliance Security Guide.
SailPoint IdentityNow Asymmetric Encryption and Key Management Documentation.
Answer : A
Yes, https://my.example.com is an example of a vanity URL. Vanity URLs are customized, branded URLs designed to be easily recognizable, memorable, and aligned with a company's branding. In this case, the subdomain my and the domain example.com create a branded, user-friendly URL. Vanity URLs are often used for simplifying access to services like IdentityNow and for improving user experience.
Key Reference from SailPoint Documentation:
Vanity URL Usage in IdentityNow: SailPoint allows customers to configure vanity URLs to provide a more personalized and branded login experience for their users.
Answer : B
https://identityNowacme.com is not typically considered a vanity URL. While it includes the 'identityNow' term, it does not appear to follow the format of a vanity URL, which generally includes a company-specific subdomain (like my) and a custom domain (example.com). In this case, the URL is more generic and lacks the branding or simplicity typically associated with vanity URLs.
Key Reference from SailPoint Documentation:
Vanity URL Structure in IdentityNow: Vanity URLs typically feature a customized subdomain that reflects the organization's branding, and identityNowacme.com does not fit this pattern.