SCP Network Defense and Countermeasures SC0-402 SCP-NDC Exam Questions
Your network was configured several years ago, with every host using a public IP address. It has been decided that NAT is to be
used when the network is reconfigured. Additionally, IPSec has been mandated as well. Which IPSec modes can be used with NAT?
Answer : A, D
The main reason you have been hired at a company is to bring the network security of the organization up to current standards. A
high priority is to have a full security audit of the network as soon as possible. You have chosen an Operational Audit and are
describing it to your coworkers. Which of the following best describes an Operational audit?
Answer : B
In your network there is an ISA server running as the firewall. It is a simple design, a single machine with two network cards. You
are configuring the Access Policies on this machine. What is the function of the Site and Content Rules section of the Access Policy?
Answer : B
Recently, you have seen an increase in intrusion attempts and in network traffic. You decide to use Snort to run a packet capture
and analyze the traffic that is present. Looking at the example, what type of traffic did Snort capture in this log file?
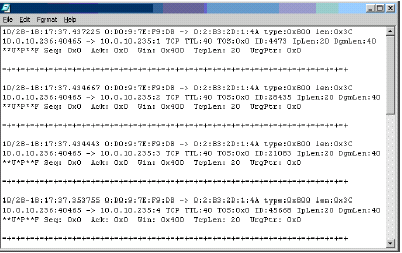
Answer : A
Recently, you have seen an increase in intrusion attempts and in network traffic. You decide to use Snort to run a packet capture
and analyze the traffic that is present. Looking at the example, what type of traffic did Snort capture in this log file?
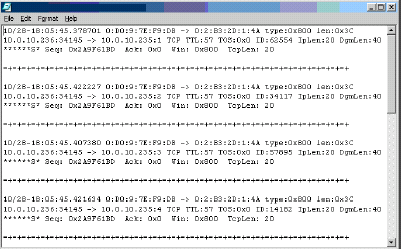
Answer : D
What should be your first step when installing Firewall-1 on a multi-homed Windows NT server?
Answer : C
You have been hired at a large company to manage network security. Prior to your arrival, there was no one dedicated to security,
so you are starting at the beginning. You hold a meeting and are discussing the main functions and features of network security. One
of your assistants asks what the function of Confidentiality in network security is. Which of the following best describes
Confidentiality?
Answer : B