Splunk Cloud Certified Admin SPLK-1005 Exam Questions
Which of the following statements is true regarding sedcmd?
Answer : D
SEDCMD in props.conf applies regular expressions to modify data as it is ingested. It is useful for transforming raw event data before indexing. [Reference: Splunk Docs on SEDCMD]
Which file or folder below is not a required part of a deployment app?
Answer : D
When creating a deployment app in Splunk, certain files and folders are considered essential to ensure proper configuration and operation:
app.conf (in default or local): This is required as it defines the app's metadata and behaviors.
local.meta: This file is important for defining access permissions for the app and is often included.
metadata folder: The metadata folder contains files like local.meta and default.meta and is typically required for defining permissions and other metadata-related settings.
props.conf: While props.conf is essential for many Splunk apps, it is not mandatory unless you need to define specific data parsing or transformation rules.
D . props.conf is the correct answer because, although it is commonly used, it is not a mandatory part of every deployment app. An app may not need data parsing configurations, and thus, props.conf might not be present in some apps.
Splunk Documentation Reference:
Building Splunk Apps
Deployment Apps
This confirms that props.conf is not a required part of a deployment app, making it the correct answer.
Which of the following is an accurate statement about the delete command?
Answer : C
The delete command in Splunk does not remove events from disk but rather marks them as 'deleted' in the index. This means the events are not accessible via searches, but they still occupy space on disk. Only users with the can_delete capability (typically admins) can use the delete command.
Splunk Documentation Reference: Delete Command
For the following data, what would be the correct attribute/value oair to use to successfully extract the correct timestamp from all the events?
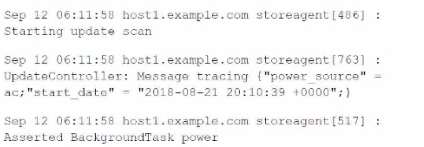
Answer : C
The correct attribute/value pair to successfully extract the timestamp from the provided events is TIME_FORMAT = %b %d %H:%M:%S. This format corresponds to the structure of the timestamps in the provided data:
%b represents the abbreviated month name (e.g., Sep).
%d represents the day of the month.
%H:%M:%S represents the time in hours, minutes, and seconds.
This format will correctly extract timestamps like 'Sep 12 06:11:58'.
Splunk Documentation Reference: Configure Timestamp Recognition
What is the recommended method to test the onboarding of a new data source before putting it in production?
Answer : A
The recommended method to test the onboarding of a new data source before putting it into production is to send test data to a test index. This approach allows you to validate data parsing, field extractions, and indexing behavior without affecting the production environment or data.
Splunk Documentation Reference: Onboarding New Data Sources
When a forwarder phones home to a Deployment Server it compares the check-sum value of the forwarder's app to the Deployment Server's app. What happens to the app If the check-sum values do not match?
Answer : A
When a forwarder phones home to a Deployment Server, it compares the checksum of its apps with those on the Deployment Server. If the checksums do not match, the app on the forwarder is always deleted and re-downloaded from the Deployment Server. This ensures that the forwarder has the most current and correct version of the app as dictated by the Deployment Server.
Splunk Documentation Reference: Deployment Server Overview
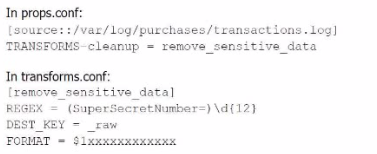
A user has been asked to mask some sensitive data without tampering with the structure of the file /var/log/purchase/transactions. log that has the following format:
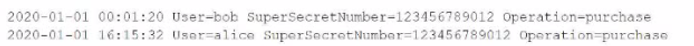
A)
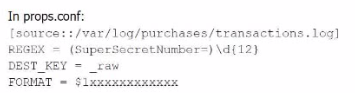
B)
C)
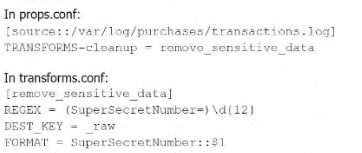
D)
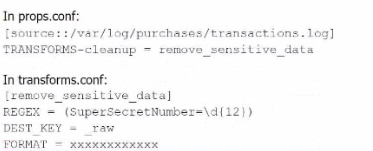
Answer : B
Option B is the correct approach because it properly uses a TRANSFORMS stanza in props.conf to reference the transforms.conf for removing sensitive data. The transforms stanza in transforms.conf uses a regular expression (REGEX) to locate the sensitive data (in this case, the SuperSecretNumber) and replaces it with a masked version using the FORMAT directive.
In detail:
props.conf refers to the transforms.conf stanza remove_sensitive_data by setting TRANSFORMS-cleanup = remove_sensitive_data.
transforms.conf defines the regular expression that matches the sensitive data and specifies how the sensitive data should be replaced in the FORMAT directive.
This approach ensures that sensitive information is masked before indexing without altering the structure of the log files.
Splunk Cloud Reference: For further reference, you can look at Splunk's documentation regarding data masking and transformation through props.conf and transforms.conf.
Source:
Splunk Docs: Anonymize data
Splunk Docs: Props.conf and Transforms.conf