Swift Customer Security Programme Assessor Certification CSP-Assessor Exam Questions
What are the conditions required to permit reliance on the compliance conclusion of a control assessed in the previous year? (Choose all that apply.)
Answer : B, C, D
Which authentication methods are possible on the Alliance Interfaces? (Choose all that apply.)

Answer : A, B, C, D
How are online SwiftNet Security Officers authenticated?
Answer : A
A Swift user has moved from one Service Bureau to another What are the obligations of the Swift user in the CSP context?
Answer : D
A Treasury Management System (TMS) application is installed on the same machine as the customer connector (such as MQ server) connecting towards a Service Bureau Are these applications/systems in scope of CSCF?
Answer : A
A Swift user relies on a sFTP server to connect through an externally exposed connection with a service provider or a group hub What architecture type is the Swift user? (Choose all that apply.)
Answer : B, D
Using the outsourcing agent diagram. Which components must be placed in a secure zone? (Choose all that apply.)
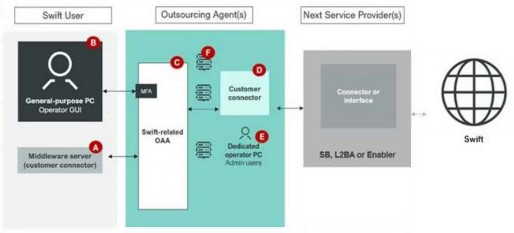
Answer : A, D