Trend Micro Certified Professional for Deep Security Deep-Security-Professional Exam Questions
Your VMware environment is configured without using NSX. How can Deep Security provide protection to the virtual images hosted on your ESXi servers?
Answer : A
Customers protecting VMware environments without NSX can use a Deep Security Agent on each of their virtual machines. By using the Deep Security Agent, the VMware environment can be pro-tected using all the Deep Security Protection Module.
protect-vmware-environments
Explication: Study Guide - page (432)
Which Deep Security Protection Modules can be used to provide runtime protection for the Kubernetes and Docker platforms? Select all that apply.
Answer : A, B, C
Container users can benefit from Kubernetes and Docker platform protection at runtime with Intrusion Prevention, Integrity Monitoring and Log Inspection rules using the Deep Security Agent installed on the host. The Deep Security Intrusion Prevention approach allows you to inspect both east-west and north-south traffic between containers and platform layers like Kubernetes.
Explication: Study Guide - page (353)
As the administrator in a multi-tenant environment, you would like to monitor the usage of security services by tenants? Which of the following are valid methods for monitoring the usage of the system by the tenants?
Answer : B
Deep Security Manager records data about tenant usage. This information is displayed in the Ten-ant Protection Activity widget on the Dashboard, the Statistics tab in tenant Properties, and the Chargeback report.
This information can also be accessed through the Status Monitoring REST API which can be enabled or disabled from the Administration > Advanced > System Settings > Advanced > Status Monitoring API.
multi-tenancy
Explication: Study Guide - page (422)
What is the purpose of the override.properties file?
Answer : B
The properties specified in this configuration file override the properties specified in the dsm.properties file. This file can be created manually by a support engineer to modify product be-havior without affecting the original configuration.
Explication: Study Guide - page (42)
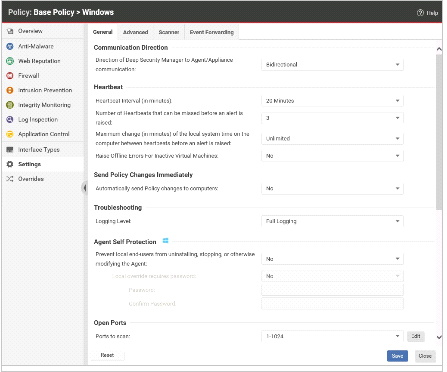
Based on the policy configuration displayed in the exhibit, which of the following statements is true?
Answer : B
The Intrusion Prevention Protection Module is enabled, its Behavior is set to Prevent and rules are assigned. When viewing the events, you notice that one of Intrusion Prevention rules is being triggered and an event is being logged but the traffic is not being blocked. What is a possible reason for this?
Answer : D
The Intrusion Prevention Protection Module is enabled, but the traffic it is trying to analyze is encrypted through https. How is it possible for the Intrusion Prevention Protection Module to monitor this encrypted traffic against the assigned rules?
Answer : A
inrusion-prevention-ssl-traffic